Intel SGX Resources
FAQ: General questions
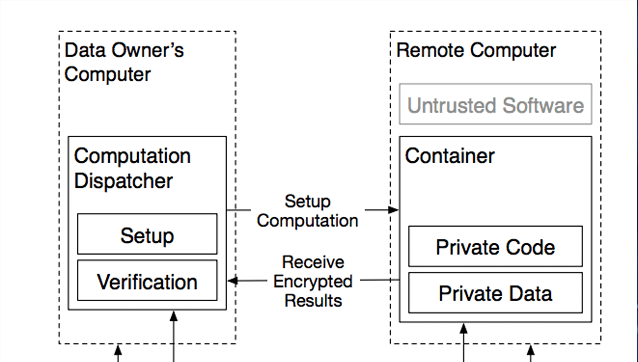
Intel® SGX is an extension to the x86 architecture that allows running applications in completely isolated secure enclaves. Intel® SGX applications are isolated from other applications running on the same system, but also from the operating system, the hypervisor, the system management module as well as the BIOS, and the firmware. The memory of secure enclaves is also encrypted to thwart physical attacks. These security guarantees prevent even system administrators with physical access to the SGX nodes from tampering with the application once it is started. Intel® SGX supports data sealing which allows enclaves to persist data securely such that the data can only be read by the enclave. Through remote attestation, Intel® SGX enables third parties to verify that an application is indeed running inside an enclave and the application has not been tampered with.
Developer questions
To develop applications that utilize Intel® SGX, Intel® provides the Intel® SGX SDK, which supports applications written in C or C++. Alternatively, the Enclave Development Platform, is an open-source SDK provided by Fortanix that enables the development of secure SGX applications in Rust. Developing enclave applications using EDP offers a number of benefits:
- Safety: EDP combines the security properties of SGX and the safety features of Rust, in contrast to other SDKs that support unsafe languages, such as C or C++. Developing enclave code using unsafe languages can lead to exposing all secrets with a single memory safety vulnerability.
- Rust compatibility: EDP applications are like Rust native applications and most Rust crates support SGX by default.
- Ease of use: EDP applications support multiple threads, network connections, and do not require explicitly defining enclave entry points or specifying the “untrusted” code of your application, since this is all provided for you.
- Abstraction: Because EDP programs look just like regular Rust programs, supporting enclave platforms other than Intel® SGX (such as AWS Nitro Enclaves) will work in the same way.