Banking and Financial Services
Deliver Modern and Secure Financial Services
Protect sensitive financial and personally identifiable information (PII), accelerate digital transformation, and stay in compliance with global regulations and frameworks. Deliver new experiences. Delight customers. Mitigate risk.
Transform Your Data Security Operations
Financial services organizations are expected to deliver seamless digital banking experiences and innovative solutions while vigorously securing sensitive data and meeting ever-evolving compliance requirements. Trusted by some of the world’s largest financial institutions, Fortanix helps to confidently secure data wherever it resides, prevent digital fraud, and advance your digital journey to enable cutting-edge financial products and services.
How Fortanix Helps
Achieve End-to-End Data Security
Fortanix enables you to secure data across all your on-prem and cloud environments. From full disk to file system to database encryption, data is protected at-rest, in-transit, and in-use with a unified platform built on confidential computing. Apply policy-driven protection with just a few clicks and achieve consistent security across all workloads. Manage your cryptographic security posture to identify exposed data services. Bring and hold your own keys to be in control over your data.

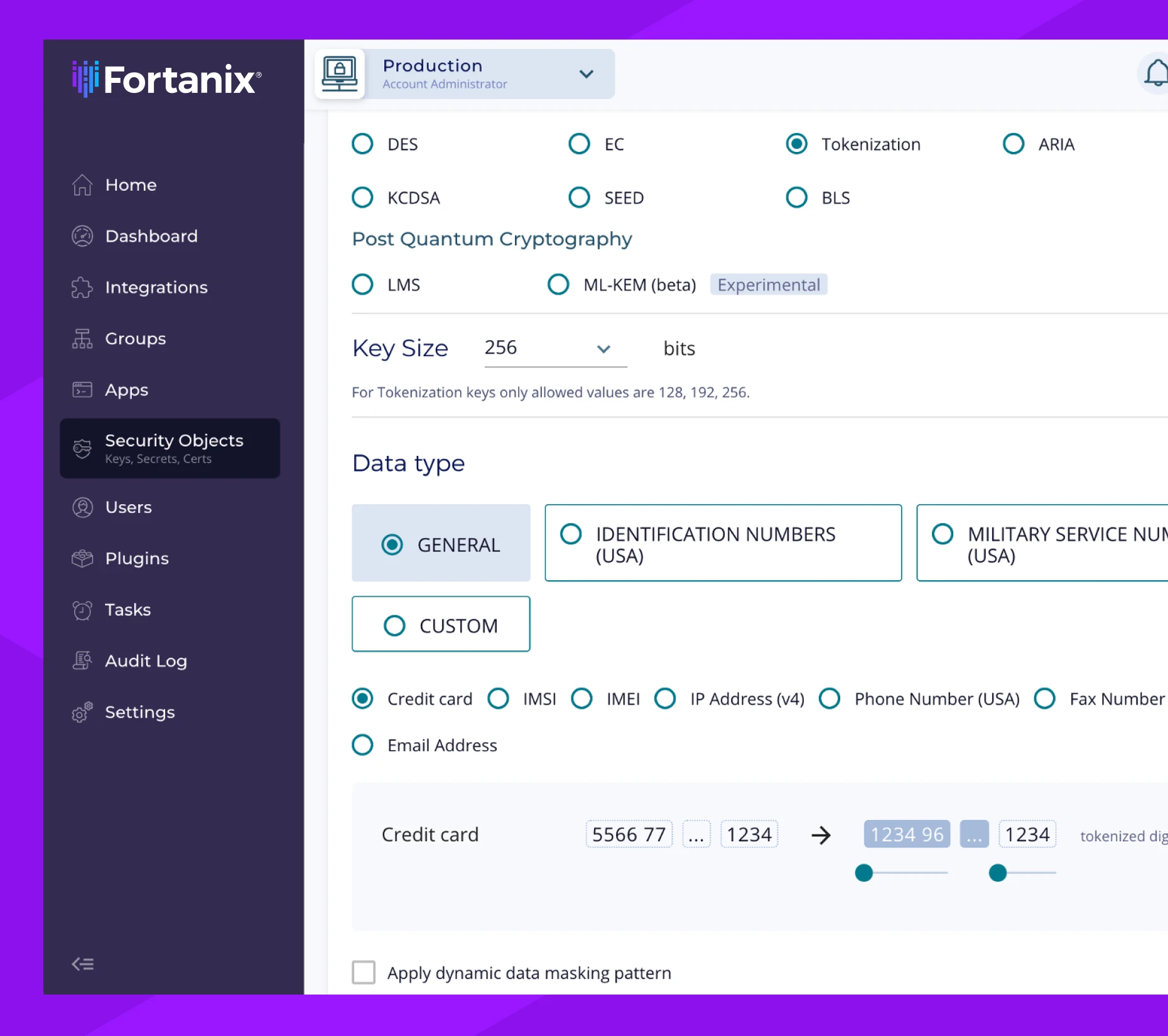
Securely Innovate with Your Data
Obfuscate payment and PII with Data Tokenization. Apply Format Preserving Encryption to employ data across applications and workflows to derive insights and build new products without compromising data security, privacy, and compliance.
Elevate Mainframe Security
The Fortanix platform simplifies cryptographic security across your entire infrastructure, including your mainframes. Fortify payment security and upgrade legacy 3DES keys to the (PQC-ready) AES standard and easily import/export X9.24/TR-31 keys from the Fortanix platform with a simple plugin.

Drive Global Compliance
Benefit from centralized visibility and control over the policies and procedures that keep your data safe with comprehensive data controls. Meet and prove compliance with regulations like, PCI DSS, GLBA, GDPR, Schrems II, and more to support customers and financial transactions around the world.

Access Controls
Leverage powerful identity and access management configurations with SSO and MFA for added security.

Data Sovereignty
Retain control and management of encryption keys to support sovereign cloud.

Automatic Attestation
Fortanix handles attestation to continuously assess and validate your systems for security.
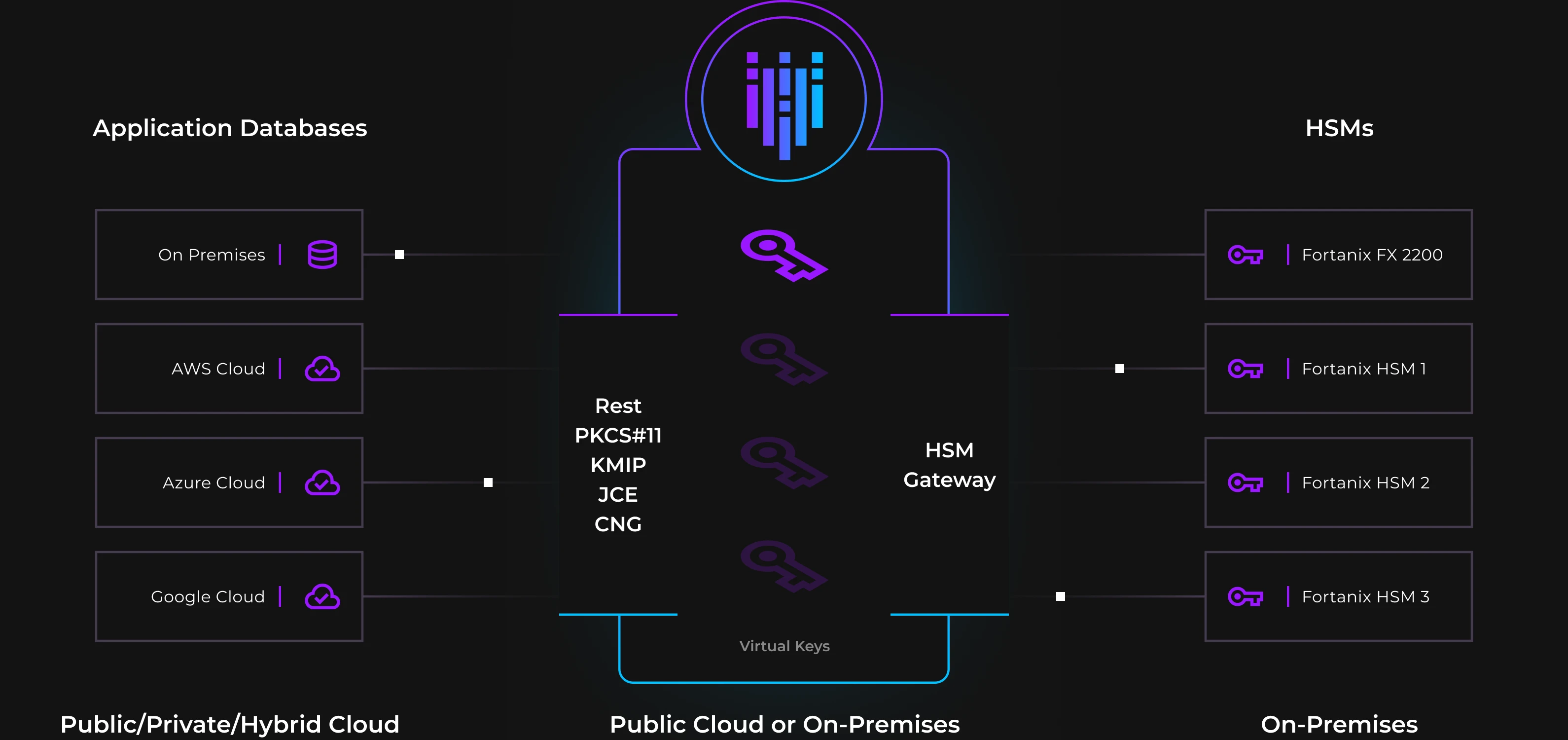
Deploy a Modern Solution You Can Trust
As you strengthen your encryption methods and close gaps in your security posture, store keys and secrets on Fortanix’s scalable, compliant solution. You can even consolidate your legacy HSMs using our secure HSM gateway. All of our appliance is FIPS 140-2 L3 validated and comes with on-prem and SaaS deployment options.
Hear from Customers and Partners
"Since Goldman Sachs was already a customer of Fortanix, we’ve seen the benefits of its technology first-hand. Every single business with sensitive data can relate to the challenges of data security and privacy, making them a potential customer of Fortanix. More importantly, we love backing mission-driven founders and Fortanix certainly has a bold vision of solving cloud security and privacy."
Soumya Rajamani
Vice President at Goldman Sachs
Featured Resource