Overview
Organizations struggle with escalating data sprawl as sensitive information—including PII, PHI, payment data, and intellectual property—scatters across on-premises systems, cloud platforms, and SaaS applications. Growing privacy regulations like GDPR, CCPA, HIPAA, and PCI DSS demand that enterprises know exactly where sensitive data resides and ensure its proper protection.
Most organizations rely on fragmented, perimeter-focused security tools that operate in silos and react to breaches rather than prevent them. This reactive approach creates significant compliance and security risks in today's dynamic digital landscape.
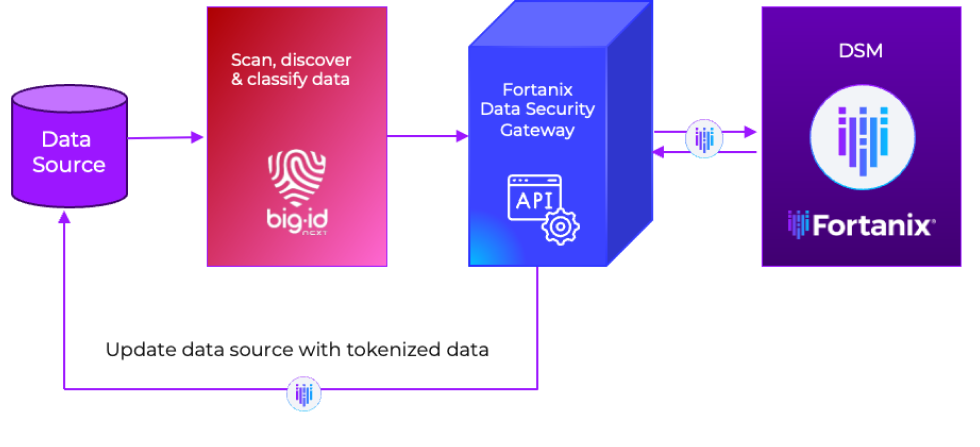
The Fortanix-BigID integration transforms this paradigm. When BigID discovers sensitive data, it automatically invokes the Fortanix Data Security Gateway, which applies policy-based encryption or tokenization through Fortanix DSM, delivering seamless, automated data protection with full auditability.
Automate Data Security at Scale
The BigID-Fortanix integration solves this fragmentation by automatically connecting data discovery with protection. Once BigID identifies sensitive PII, the integration automatically triggers Fortanix's encryption services through a secure communication channel, eliminating manual intervention. The solution leverages BigID's classifiers to create security objects in Fortanix DSM, then applies policy-driven tokenization or encryption while maintaining complete audit trails. This closed-loop system delivers continuous, automated data protection from discovery to implementation.
Fortanix Solution
The integration unites BigID’s data discovery and classification with Fortanix’s data-centric protection, creating a proactive, automated security fabric.
- Discovery: BigID identifies and tags sensitive or regulated data across all environments.
- Protection: Fortanix Data Security Gateway automatically retrieves credentials, connects to the data source, and applies format-preserving tokenization or encryption through Fortanix DSM APIs.
- Governance: Once data is protected, BigID is updated to maintain synchronized visibility and avoid redundant scans.
- Deployment: Works across on-premises, cloud, and hybrid infrastructures for consistent, policy-driven protection everywhere data resides.
- Result: A unified, intelligent, and automated data-protection ecosystem that minimizes risk, eliminates manual steps, and ensures ongoing compliance.
Key Capabilities

Discover, classify, and secure—all kinds of data, wherever it resides. Dark data, hidden data, duplicate data at rest, in motion, or in use.
Flexible deployment models including on-prem subscriptions or SaaS.
Apply classification, risk scores and policies mapped to compliance regulations worldwide.

Tokenize, encrypt, and manage secrets of various data formats at scale.

Protect against audits, compliance, findings for unsecured data.
Customized policies based on security posture and use case.
Audit logs for both key management and policy enforcement.
Top Benefits

Continuous, Automated Protection
Automatically discover and protect sensitive data the moment it’s identified—no manual intervention required.

Unified Security & Compliance
Centralize policy management and maintain full audit trails to meet mandates like GDPR, CCPA, HIPAA, and PCI DSS.
Operational Efficiency at Scale
Streamline data-protection workflows with built-in automation, reducing time, complexity, and cost.

Preserve Data Utility
Fortanix’s format-preserving tokenization maintains data usability and compatibility while keeping information secure.
Summary
Together, Fortanix and BigID are helping complex organizations secure crown jewel data while democratizing it for greater business value.
The partnership aligns Fortanix's rich data security features to define and enforce how data is protected, with BigID's innovative capabilities to discover and classify what datasets should be protected—essentially enabling businesses to tap into their data’s full-potential.
About BigID
BigID empowers organizations to know their enterprise data and take action for data-centric security, privacy, compliance, AI innovation, and governance. Customers deploy BigID to proactively discover, manage, protect, and get more value from their regulated, sensitive, and personal data across their data landscape.











