Full Protection for AI Models and Enterprise Data.
Secure what matters most! Fortanix Confidential AI delivers end-to-end protection for proprietary frontier models, sensitive data, and inference across the full AI lifecycle. The joint Fortanix-NVIDIA solution, built on Confidential Computing, keeps both sensitive data and model IP encrypted and inaccessible to the underlying infrastructure. Enterprises now can run advanced AI where their data resides, while model providers keep their critical IP fully protected.
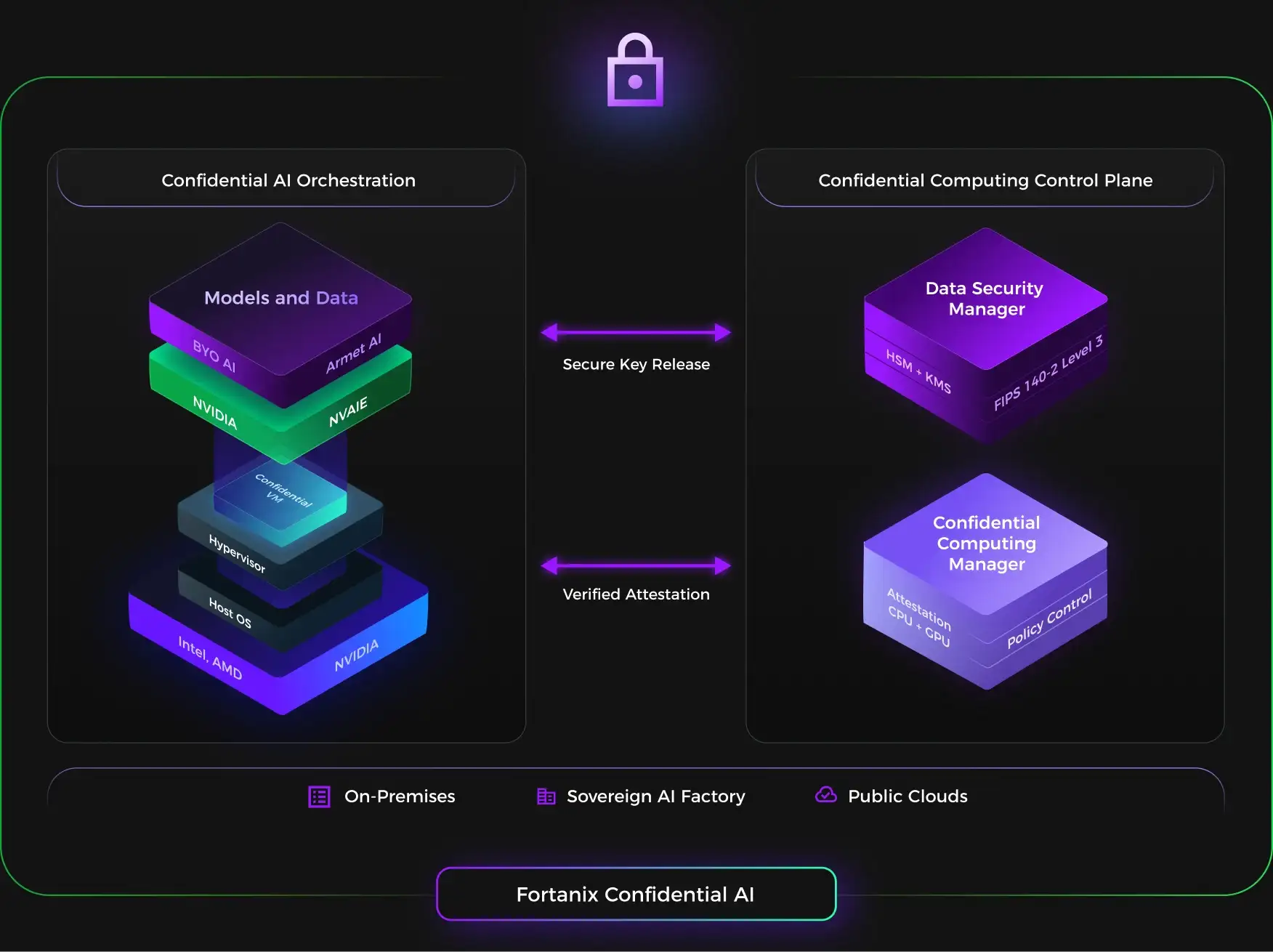
Secure Environment for AI Workloads
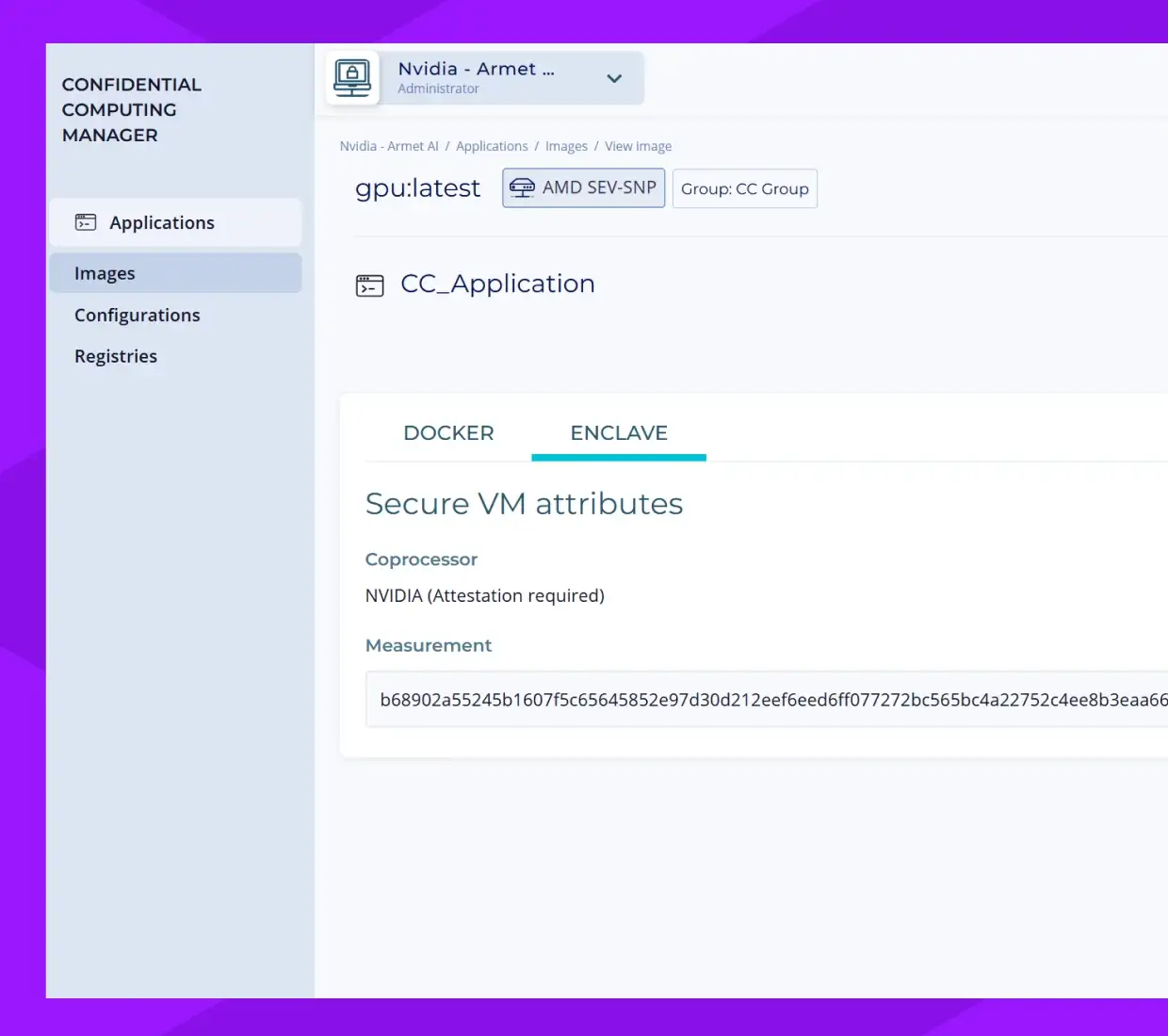
Trusted Execution Environments (TEEs) use hardware-enforced isolation and cryptographic attestation to create secure enclaves independent of the host system. CPU and GPU memory encryption keeps sensitive data, model weights, and inference protected in memory—even from privileged insiders, hypervisors, and co-resident workloads. Use the TEE to
- Bring Your Own AI—models, data, applications
- Deploy Armet AI—turnkey Agentic AI platform
Verifiable Infrastructure Integrity
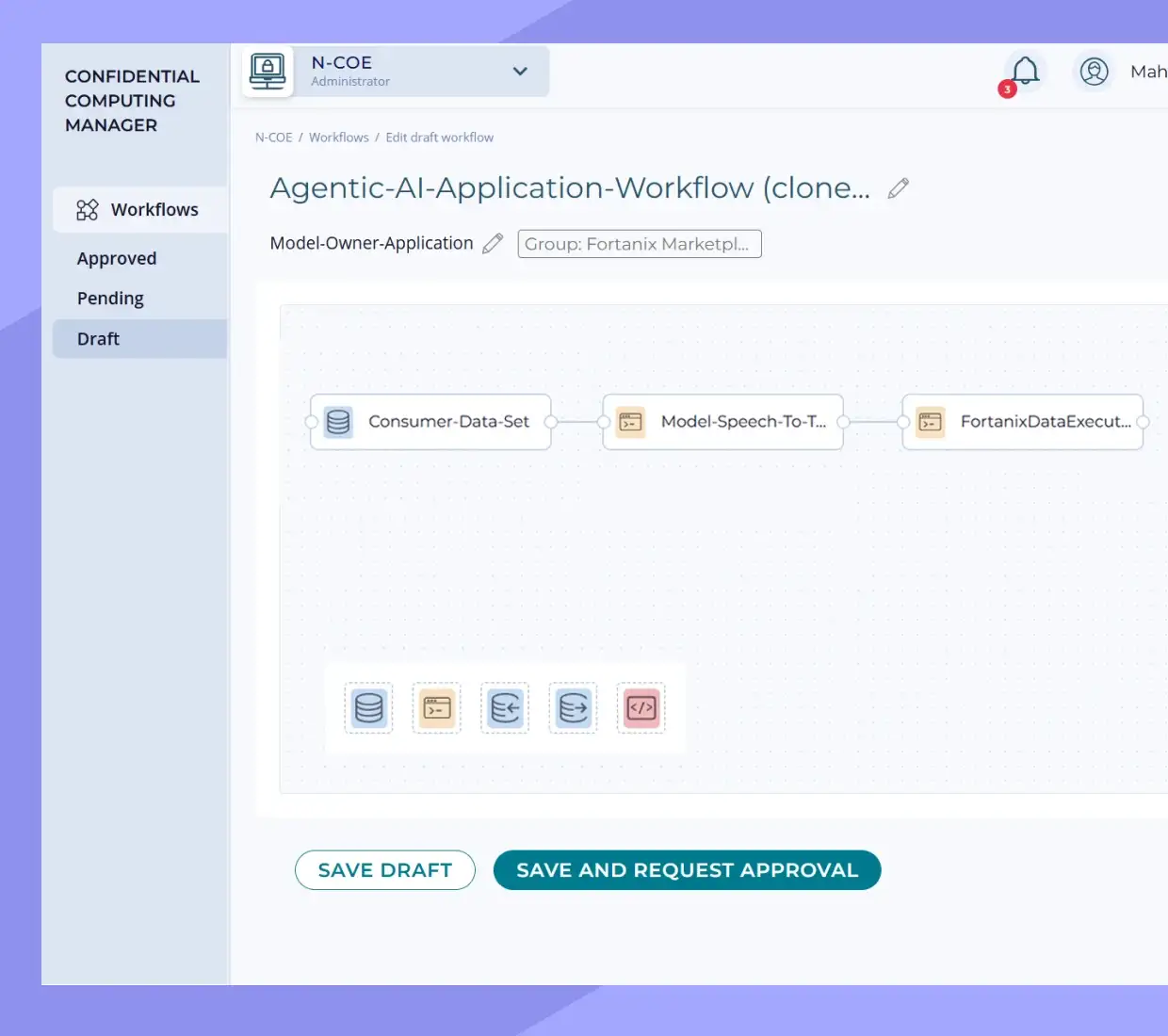
Composite attestation for CPU and GPU create a single chain of trust. Verify exactly what AI workload is running with hardware-signed proof. The confidential control plane allows you to
- Create Confidential VMs and Containers
- Set policy controls
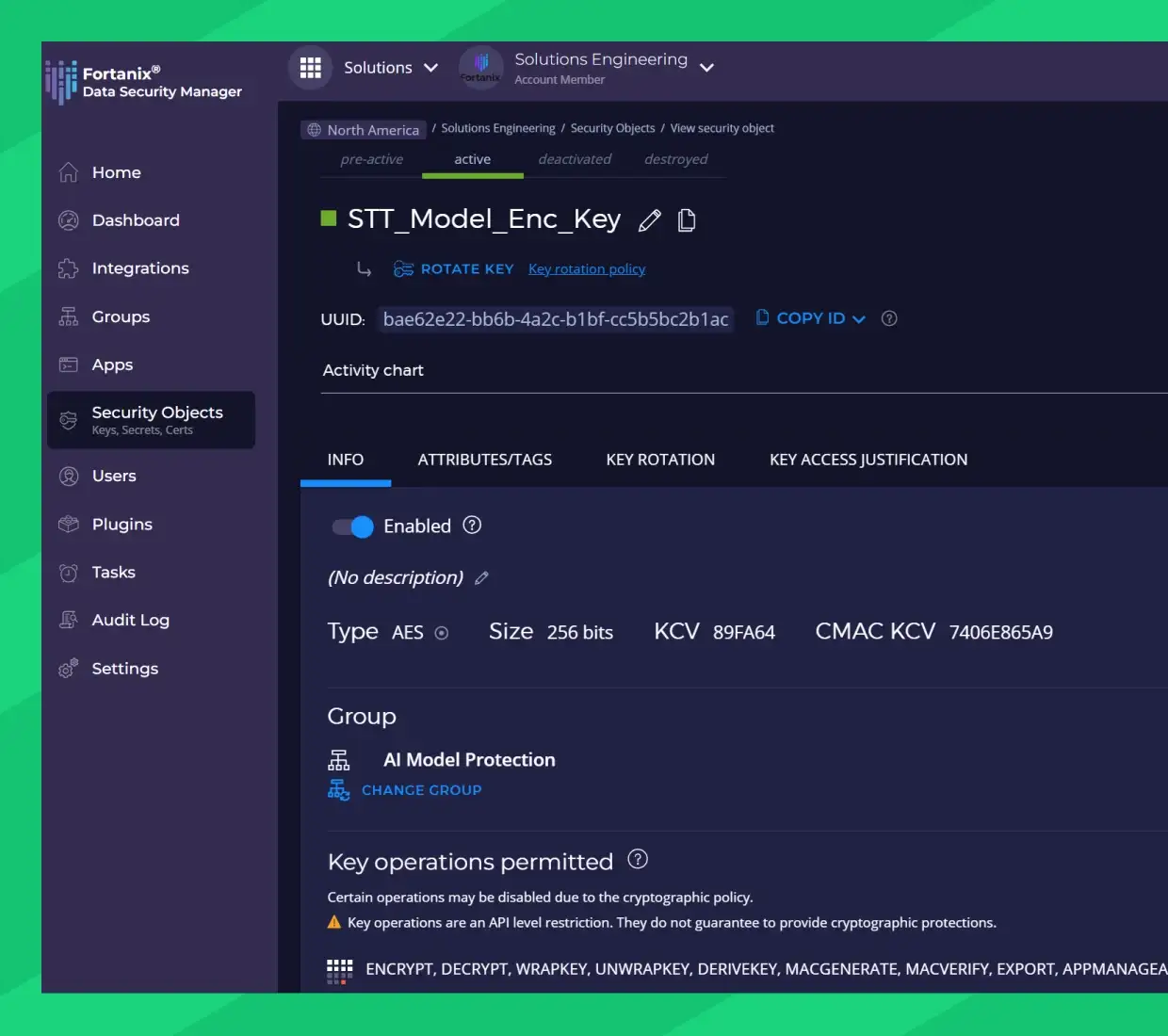
Secure Key Release
Access to datasets and model artifacts is allowed only after verified attestation. Decryption happens only within verified, isolated environments. Drive crypto agility with
- FIPS 140-2 Leve 3 Certified HSM with built-in KMS
- Latest NIST-approved PQC algorithms
Benefits

Expand your business, while securing your IP anywhere it runs. Keep model, weights, and configuration confidential, from inception through deployment.

Keep sensitive data encrypted while in use and maintain regulatory compliance.

Enable AI innovation across regulated industries and sensitive use cases with a zero-trust security model.
Use Cases

Healthcare & Life Sciences
Process patient records, genomic data, and clinical trial information while maintaining HIPAA compliance and patient privacy.

Financial Services
Process patient records, genomic data, and clinical trial information while maintaining HIPAA compliance and patient privacy.

Government & Defense
Deploy AI for intelligence analysis and national security applications with cryptographic guarantees that meet the highest classification levels.

Enterprise AI
Protect proprietary models and business-critical data while deploying AI across hybrid cloud, multi-cloud, and edge environments.

AI Model Providers
Monetize your AI models by deploying them to customer environments without revealing model weights or risking intellectual property theft.
Resources
Here are some of latest news, blogs, resources, events, and more