Overview
As integrating security in every stage of the software development lifecycle (SDLC) gains momentum—secrets management is fast emerging as the most pivotal DevSec Ops element to ensure security at all stages of SDLC.
If left unchecked, the secret sprawl that comes with cloud-native development and multicloud infrastructures can snowball into a significant problem for the DevOps teams that lean on multiple disparate tools for securing different phases of the development process.
What's required is a centralized system that can integrate with all these tools and systems, as most Cloudnative secrets management tools are limited to the specific cloud provider and fail under a multi-cloud scenario.
Fortanix Solution
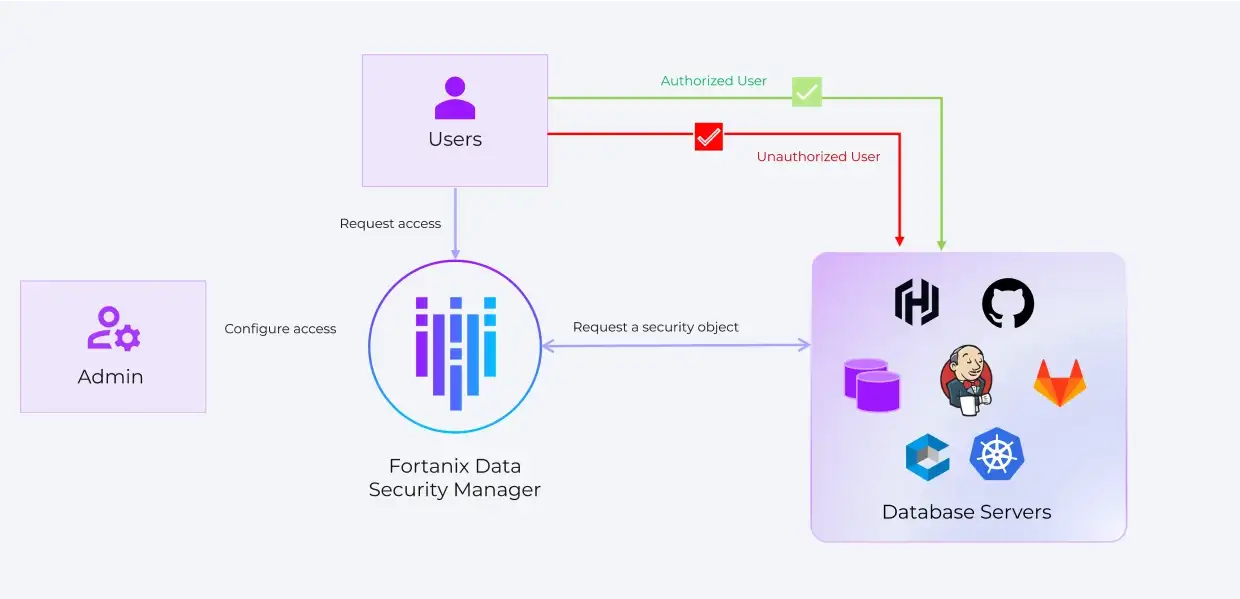
Fortanix provides a single centralized platform to securely store, control and manage secrets outside the source code in a FIPS 140-2 level 3 certified HSM. With flexible deployment modes and scalable architecture, Fortanix secret management works across environments, on-premises, natively in the cloud, hybrid and multicloud. Moreover, it can integrate with any DevOps environment with Rest APIs.
Benefits

Fortanix can manage secrets natively in the cloud and on-premises, providing extensive RESTful APIs through open standards such as OAuth, OpenID (SAML), LDAP, JWT, and PKI. Integrates with any DevOps environment with Rest APIs. Supports upcoming technologies like Kubernetes, Docker etc.

Secured with Intel® SGX and built using Fortanix patented Runtime Encryption® Technology, Fortanix runs every operation in HSM-grade security, ensuring complete control over your keys, data and secrets. Comprehensive audit logs provide insight into how secrets are being used, helping you meet compliance.

Unifies key management operations with role-based access controls. Prevents unauthorized password change and alerts on simultaneous logins by same user.
Key Differentiators

Unified platform for Data Security
A unified platform for to simplify and facilitate centrally managed secrets, keys, and tokens.

Enable operational efficiency
Identify how well your data is protected and how it aligns with current security policies. With an intuitive dashboard, Fortanix helps identify and prioritize where and when to apply new quantum-proof algorithms.

Lower costs with increased efficiency
Fortanix enables organizations to own and control the lifecycle of all encryption keys. Crypto-agility accelerates the deployment of quantum-proof algorithm standards. Fortanix supports the latest NSA-recommended quantum-resistant algorithms and rapidly implements the latest NIST standards into its SaaS platform.
Resources
Here are some of latest news, blogs, resources, events, and more