Secrets management is critical to business operations because organizations can track users or machines trying to access sensitive data for operational purposes. Generally, secrets include usernames, passwords, certificates, API keys, Secure Socket Shell (SSH) keys, and encryption keys.
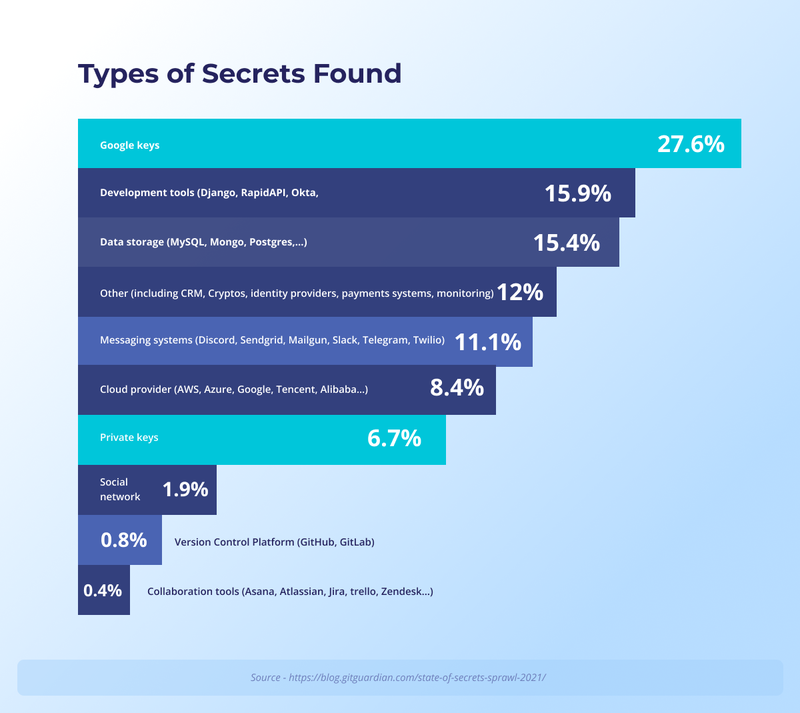
Poor secrets management setup leads to secrets sprawl (secrets embedded as plain text into the source code) that attackers can easily exploit for ransomware. The 2021 State of Secrets Sprawl report by GitGuardian indicates an alarming growth of 20% year-over-year in the number of secrets found.
The 2021 Annual Threat Monitor from NCC (National Computing Centre) Group, UK, a global expert in cyber security and risk mitigation, reports 2,690 ransomwares in 2021, a 92.7% increase compared to 2020. According to the Gartner audit plan, ransomware is the main risk area that audit departments should focus on in 2022.
Secrets Management Challenges in Multi-Cloud
When organizations migrate to the cloud, data access and transfer becomes challenging under the law compliance.
- Developers, applications, and infrastructure systems share secrets for operational purposes, which often results in secrets sprawl. This phenomenon is also known as hardcoding, where organizations lose control and visibility over the distribution of secrets. As a result, attackers can get their hands on leaked data.
- Secrets help identify the users wanting to access data; however, in a cloud environment and automation, secrets are used to identify machines or applications trying to access data.
- Legacy Hardware Security Modules (HSMs) are mainly used to secure encryption keys, but they lack the efficiency of protecting different types of secrets in a cloud infrastructure.
- Other traditional secrets management tools are not DevOps friendly because they do not offer encryption of API keys, dynamic secrets generation, containers & microservices, and rotation within multi-cloud services.
Organizations need an ultimate Data Security Manager to overcome the existing limitations and protect sensitive data. An effective secret management solution tracks and audits the user/machine access continuously, facilitates key rotation, limits data exposure, separates data from secrets, and in the case of a secret sprawl, helps security teams understand the duration of the threat.
How Fortanix Helps Organizations
Fortanix's Data Security Manager (DSM) manages secrets natively in the cloud and on-premises, providing extensive RESTful APIs through open standards such as OAuth, OpenID (SAML), LDAP, JWT, and PKI. The solution securely stores, controls, and manages secrets outside the source code in a FIPS 140-2 level 3 certified HSM.
Below are 10 "key" advantages of Fortanix DSM to understand how the solution helps organizations have complete control over managing secrets and meet compliance requirements.
Fortanix DSM Secrets Management Advantages
- Single Pane View: Fortanix DSM provides a single pane view for unified auditing, access controls, and policy management. Organizations can detect potential risks by continuously assessing secrets usage. The centralized location helps mitigate secrets sprawl.
- FIPS 140-2 Level 3 Compliant: Authentication and Authorization are managed with direct communication to the Fortanix HSM (Hardware Security Module), which is highly secured with Intel® SGX and built using Fortanix patented Runtime Encryption® Technology. This mechanism is tamper-proof and is FIPS 140-2 level 3 compliant, a federal government mandate.
- Complete Encryption on Servers/Databases: Secrets are stored on Fortanix HSM and not exposed or stored in cleartext on servers/databases. As a result, any individual, machine, or software having access to the version control system cannot access secrets. Software teams use version control systems to track the changes in the code and computer programs.
- Login Verification: Fortanix DSM API Authentication requires users to verify their identity and receive a unique token to access a network, resource, or application. This extra security layer helps mitigate the risks of weak-login credentials for password-based authentication.
- High Availability/Disaster Recovery: Fortanix DSM delivers High Availability (HA), Disaster Recovery (DR), and automated load balancing capabilities. The solution is built to scale horizontally and vertically as the demand for managing keys and secrets increases. As a result, organizations can seamlessly scale their resources per business requirements without worrying about latency and downtime.
- Role-Based and Attribute-Based Access Control: Fortanix DSM provides Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC) controls with tamper-proof audit logs. Each secret stored in DSM is associated with its creator and is stored in a specific "Group." Users can access secrets as per their role/privileges and association with that Group. There is also a provision for a quorum approval policy.
Security teams can add additional users to a Group at any time. In addition, they can map the Groups in DSM to external Active Directory (AD) groups via an external role mapping feature that further allows AD group based RBAC. As a result, security teams can quickly inspect (through the GUI or REST API) who is the creator of a secret and which other users are in the Group (and their roles). - Cryptography and Key Management: The solution protects sensitive data at rest and in transit using various cryptography applications. The cryptographic capabilities are possible by having unique key material. The comprehensive solution with the inbuilt capabilities helps security teams have a single tool to secure the data anywhere in the network.
- Plugin Library (PL): Fortanix allows programmatic rotation and dynamic secrets through the extensible DSM Plugin Library (PL). Organizations can create local copies of the plugins in the library and invoke the ones they intend to use. The plugins can be used to develop a use case-centric custom code and connect to a larger ecosystem to increase business operations efficiency.
- DevOps Apps Integration: Fortanix DSM provides several integration connectors for modern DevOps applications such as Jenkins, GitHub, GitLab, GPG, Kubernetes, etc. These connectors combine the entire business ecosystem to minimize workflow complexity and automate business operations. In addition, the integration helps systems interact with each other by exchanging data to develop business intel. As a result, organizations can be more agile and stay competitive within marketplaces.
- Confidential Computing: Fortanix DSM, powered on Confidential Computing technology, is the most secure way to distribute and use secrets at runtime. It protects data and applications in memory with non-extractable keys. It means an organization can encrypt data in transit and will be the sole owner having access to the keys. Confidential computing technology secures data across its entire lifecycle, i.e., creation, sharing, distribution, expiration, and revocation.
Fortanix DSM provides a simple and intuitive user interface. Other secrets management solutions are software-based, so organizations must deploy and manage them to keep systems running and optimized. Fortanix DSM can be deployed as a SaaS with nothing to deploy and manage.
But, even for on-prem, Fortanix has capabilities that provide a true private cloud experience. As a result, security teams only have to rack and stack hardware and never worry about updating OS, fixing database corruption, memory issues, etc.
Fortanix DSM is a powerful yet straightforward solution for enterprises and DevOps to centralize the storage and management of security artifacts.











