The Challenge
Regulations like the Schrems II ruling and GDPR require organizations to be able to revoke data access at any time, and to segregate encryption keys from data on the cloud. An external key store (XKS)—sometimes called a Bring-Your-Own-Key-Management-System (BYOKMS)—introduces an extra encryption layer to give organizations full control of their keys. With Fortanix DSM, organizations can centrally manage the key lifecycle, with granular access control and comprehensive logs to simplify the auditing process.

Fortanix Solution
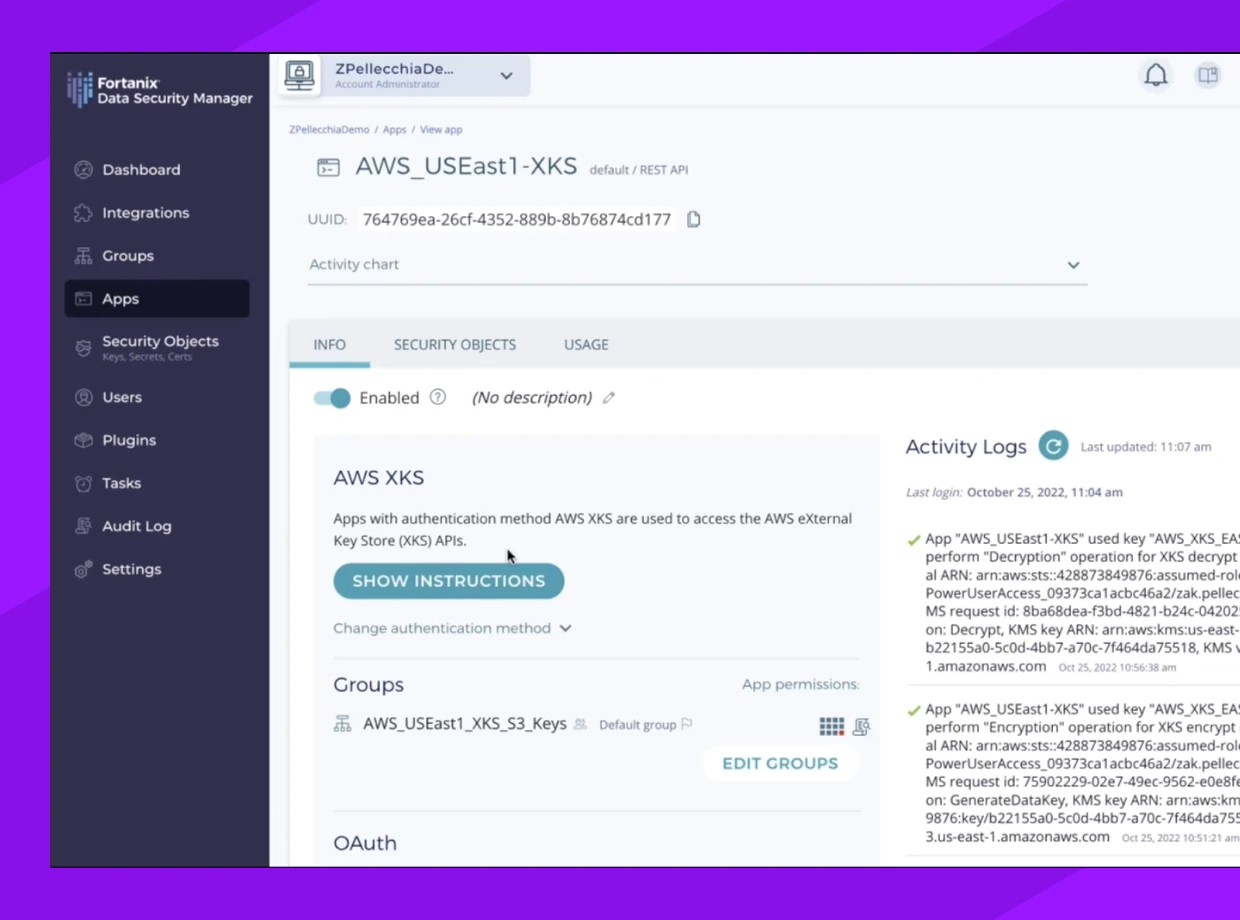
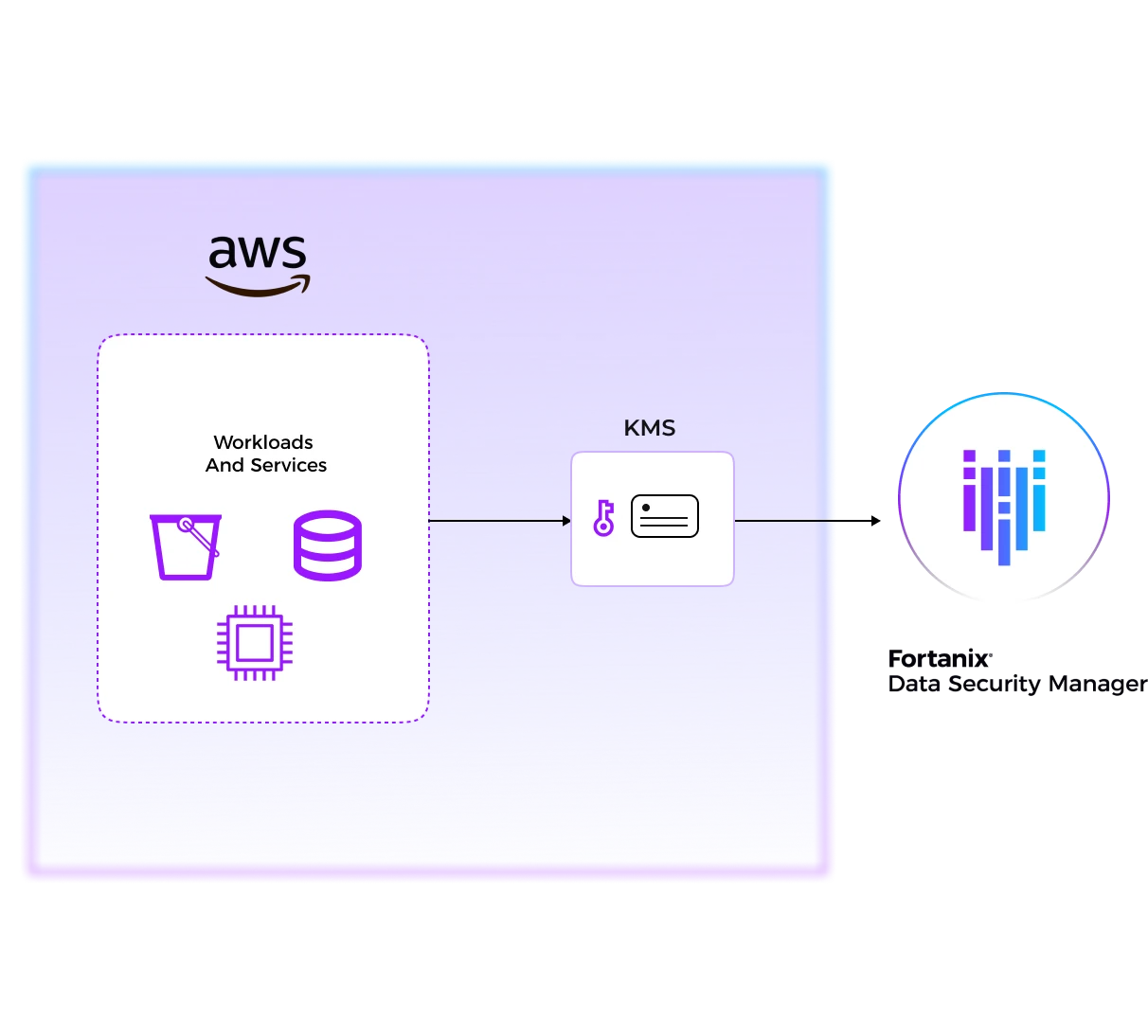
Fortanix DSM functions as an external key store aka XKS for AWS to enable organizations to move the data to the cloud with the highest level of security and control for their keys. Encryption keys are under complete customer control and secured by FIPS 140-2 level 3 certified HSMs, segregated from the cloud data. Fortanix DSM users get a centralized solution to get control the lifecycle of their keys, no matter if they are used on-premises, or in the cloud.
Benefits

Compliance mandates such as GDPR/Schrems-II require organizations to store keys separately from the data it protects. Fortanix helps meet compliance by giving customers control of their keys with FIPS 140-2 Level 3 certified hardware security modules (HSMs). Fortanix has dedicated datacenters in the European Union (EU) and can guarantee that keys remain within the EU boundaries, as per GDPR mandate. With an additional corporate entity established in The Netherlands, Fortanix operates outside USA jurisdiction to further protect the data of European citizens.

Organizations that want to fully control their risk must have full control of the keys that protect their data. By using the KMS solution from their cloud provider, they trade proximity for exclusive control. Cloud providers can be forced by a court order to hand over keys and data. With DSM as an external key store (XKS), organizations have full control and ownership of their keys and data. To further meet regulation mandates, Fortanix DSM also provides a kill-switch functionality. This allows administrators to immediately block access to data-at-rest on the GCP platform with just a couple of clicks to change permissions for any, or specific, instances and locations.

Define, enforce, and track data access policies from a single interface, and accelerate cloud migration. Fortanix DSM provides a single and secure source to protect keys and data, regardless of whether they are used on-premises, or in the cloud. DSM provides granular, role-based policies, including quorum approvals, and integrates seamlessly with existing authentication identity providers.
Key Differentiators
Immediately identify the most important risks, and drill down into the details.

Secure and Flexible deployment
Deploy as a SaaS for fast integration and scale, protecting keys with FIPS 140-2 Level 3 HSMs.

Dedicated EU data centers and corporate entity
Subpoena-proof, outside USA jurisdiction.

Unified platform for Data Security
A centralized SaaS solution to simplify and strengthen data security across hybrid and multicloud environments.
Resources
Here are some of latest news, blogs, resources, events, and more