Container images have revolutionized the world of software development and deployment, but they've also become a prime target for cyber-attacks. Threat actors often disguise their harmful code as legitimate software, leading unwitting users to install malicious container images.
To combat these risks, container engines and registries support image signing and verification. Image signing allows publishers to add digital signatures, offering consumers a means to verify a container image's integrity and authenticity.
Background of Image Signing
Before diving into container image signing, let's take a step back to explore the fundamental concepts and how various pieces fit together:
TUF: The Update Framework
TUF, short for "The Update Framework," is a comprehensive framework designed to safeguard software distribution and update systems. It minimizes the impact of key compromises and defends against various types of attacks on software update systems.
TUF achieves this by incorporating metadata containing information about trusted signing keys, cryptographic hashes of files, metadata signatures, version numbers, and expiration dates.
This creates a record that can be checked to verify the authenticity of update files. TUF identifies, downloads, and validates updates against the metadata it obtains from the repository.
Notary
Notary serves as an implementation of TUF and simplifies the secure publication and verification of content. Notary consists of two key components: Notary signer and Notary server.
The signer manages private keys and handles all signing operations. Publishers can securely sign their content offline, and once ready to make it available, they can push their trusted signed collection to the Notary server.
Consumers, having obtained the publisher's public key, can then interact with any Notary server or mirror, relying solely on the publisher's key to assess the validity and integrity of the received content.
Docker Content Trust (DCT)
Docker Content Trust builds upon Notary's feature set, enabling users to verify the integrity and authenticity of docker images. Image publishers can sign their images, and consumers can ensure that the images they pull are signed. Within the Docker CLI (command line interface), users can sign and push a container image using the $ docker trust command syntax.
Image Signing and Verification
The typical image signing, and verification process encompasses the following steps:
- Creation of Public/Private Key Pair: The private key is used for image signing and must be stored securely, as theft can have severe consequences. The public key is used for image verification.
- Signing the Image: This step is undertaken by the image publisher, who signs the container image using their private key.
- Signature Verification: Image consumers verify the image's signature using the publisher's public key to ensure an image’s integrity and authenticity.
How Fortanix Helps
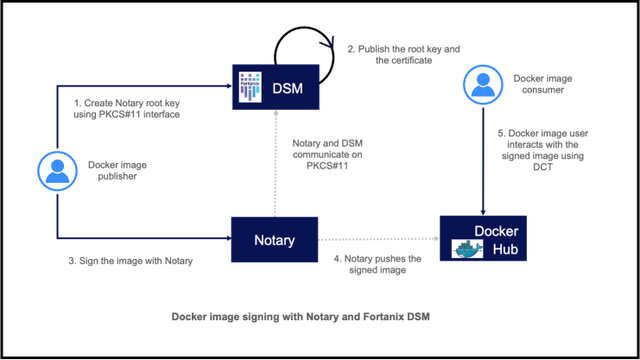
Image signing, and code signing in general, is a critical operation in the software development cycle. The importance is underscored by code signing [source] requirements set forth by the CA/Browser Forum, which necessitates vendors to "protect Private Keys in a Hardware Crypto Module conforming to at least FIPS 140-2 level 2 or Common Criteria EAL 4+." This is where Fortanix steps in, offering a market leading Hardware Security Module (HSM) integrated with Docker Notary, using Fortanix PKCS#11 library.
By following the steps outlined in the Fortanix user documentation, you can sign your Docker images with confidence. With Fortanix, you not only meet the stringent requirements of the CA/Browser Forum regarding key protection, but you also gain access to enterprise capabilities that enable secure key lifecycle management and auditing of signing operations.
Give it a try, and if you have questions or feedback, don't hesitate to reach out to us at fortanix@support.com. Fortanix is here to ensure the integrity, authenticity and safe use of your docker images.










