Overview
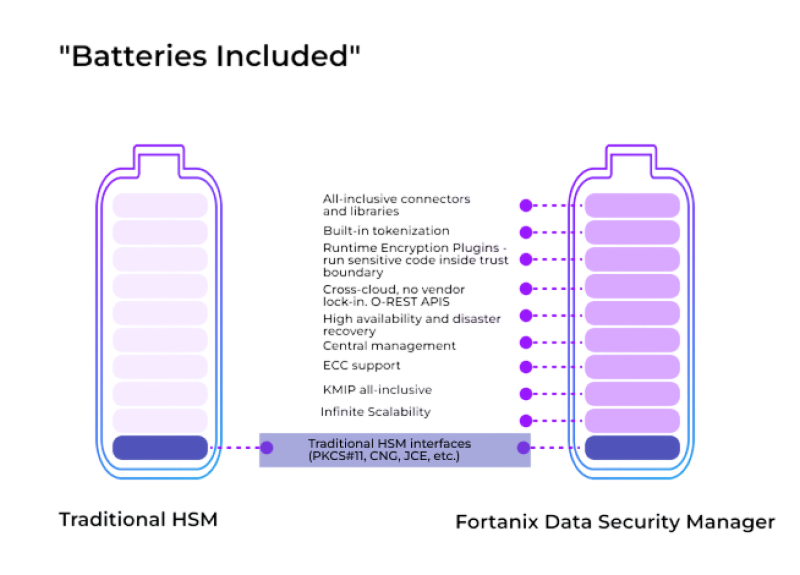
Fortanix Data Security Manager (DSM) is the world’s first solution to provide HSMgrade security with software-like flexibility. Built from the ground up for modern cloud-scale applications, Fortanix Data Security Manager (DSM) provides REST APIs alongside traditional interfaces, native server-side clustering, centralized management, a tamper-proof audit log, and more! Finally, you can secure your keys, both on-premises and in the cloud, without needing a specialized HSM talent force or unreliable and costly professional services!
Your developer will love to use REST APIs, your existing infrastructure will work with PKCS#11/KMIP, and your CIO will love centralized tamper-proof logging! IT loves zero-touch server-side clustering and built-in HA/DR.
Our transparent per-server pricing includes all connectors and all features to operate the world’s most secure KMS.
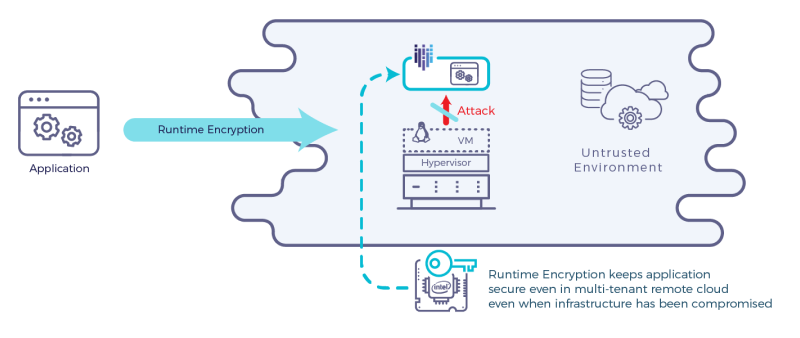
Fortanix Data Security Manager (DSM) leverages Intel® SGX to ensure that no cloud provider, service provider, or even Fortanix, has access to any of your keys and data. This ensures your keys remain protected even with malicious insiders, compromised cloud providers, or government compulsion!
Next generation HSM/KMS for Cloud Scale Applications

Provable, deterministic security from cloud provider and government subp.oena

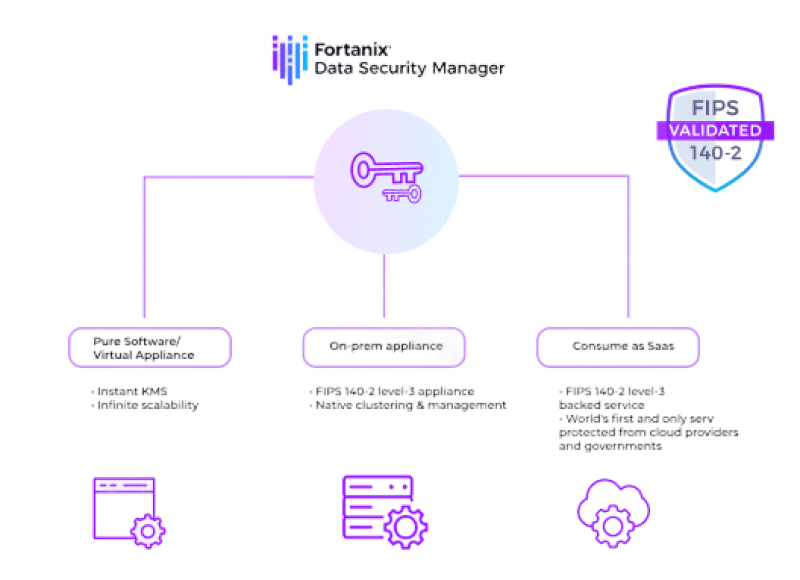
Offered as both Saas and as on-prem applications

Massive scale, multi-site, multi-tenant, highly-available, disaster recovery

FIPS 140-2 level-3 appliance. Also available as pure software virtual HSM without FIPS certifications
Why ?
With all the madness of the cybersecurity world, we believe customers need better control of their destiny. Fortanix provides you the following:
- GUARANTEED SECURITY: Fortanix security cannot be subverted by any malicious insider, root user, cloud provider, network intruder, OS-vulnerability, government compulsion or subpoena! You get cryptographic certainty against these threat vectors.
- PREVENTIVE SECURITY: Fortanix prevents attacks from happening, rather than generating alerts for you to manage after the fact.
- NO-BS MESSAGING: No software can provide protection from all types of vulnerabilities as that would violate the Halting Problem. We make sure you understand the attack vectors that we cannot protect against before you deploy our solution!
How?
Fortanix created Runtime EncryptionTM technology to keep your application encrypted even when it runs. Fortanix provides this real-time encryption of all memory and software stack with negligible performance penalty and even in a multi-tenant cloud environment. All the keys and security needed to manage Runtime Encryption are kept secure in Intel® SGX hardware. Runtime Encryption protects your applications from all types of software attacks originated by OS, network intruders, privileged users, etc.
What?

Fortanix Data Security Manager
Next generation HSM/KMS for internet scale applications.
Now publicly available!

Database Security
Run databases while never decrypting data or queries outside the trust boundary. Run analytics with sensitive private data without having access to the data!
Trials with selected design partners

Machine Learning
Train your model with sensitive data without having access to that data! Protect your trained model from code theft.
Trials with selected design partners










