Secure AI Workloads
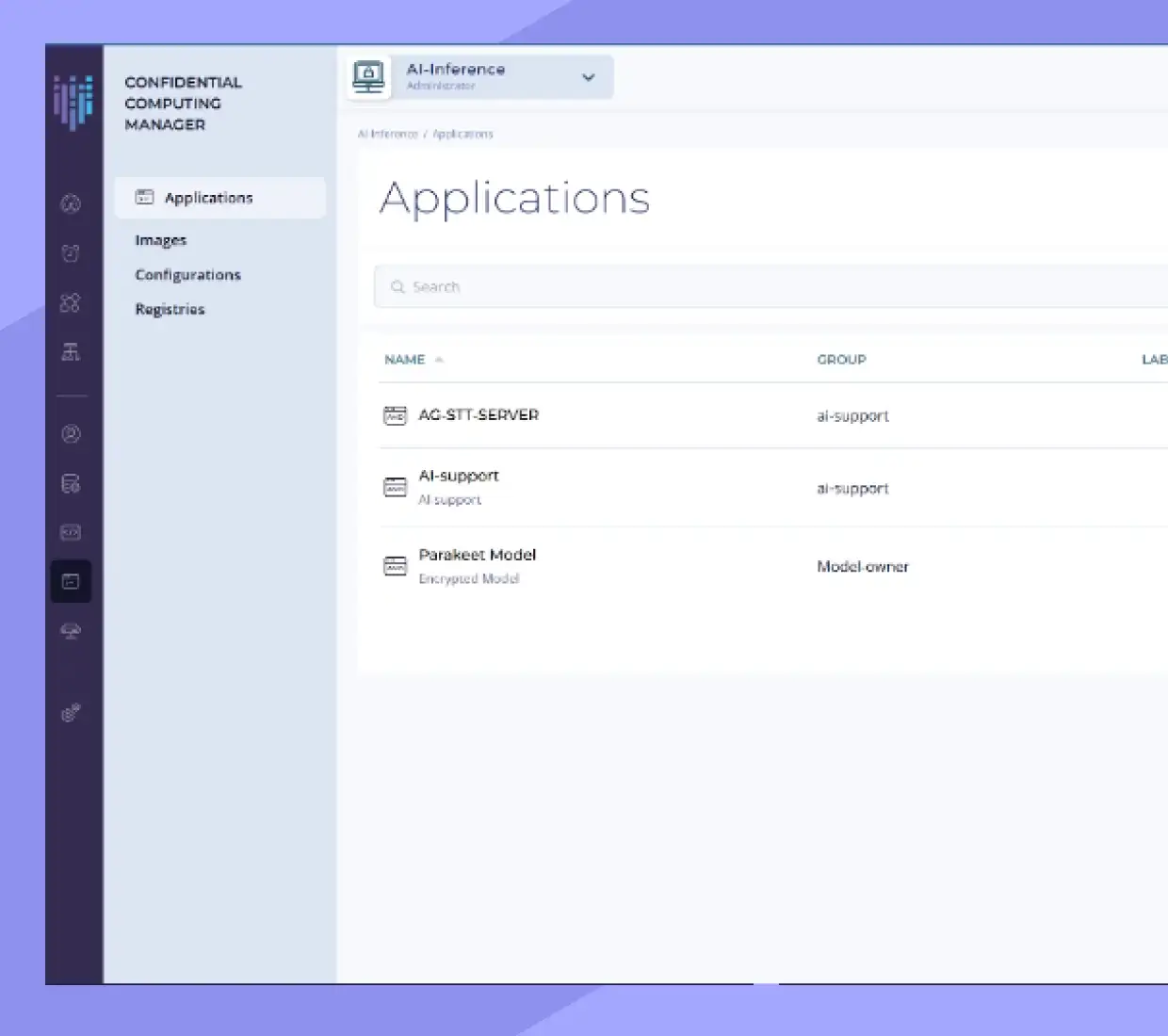
Create and manage Trusted Execution Environments to enforce security, sovereignty, and compliance across your AI infrastructure. Use a single control plane to configure, attest, and monitor your entire Confidential Computing stack, CPUs and GPUs. Eliminate operational complexity, the risk of unauthorized access, and exposure of data and AI models while in active use.

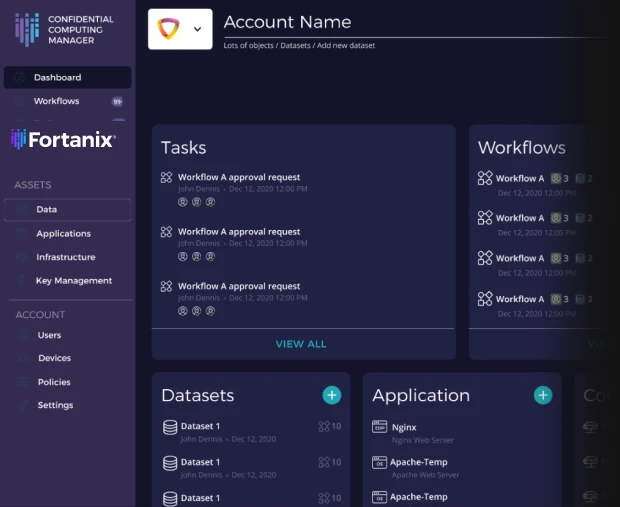
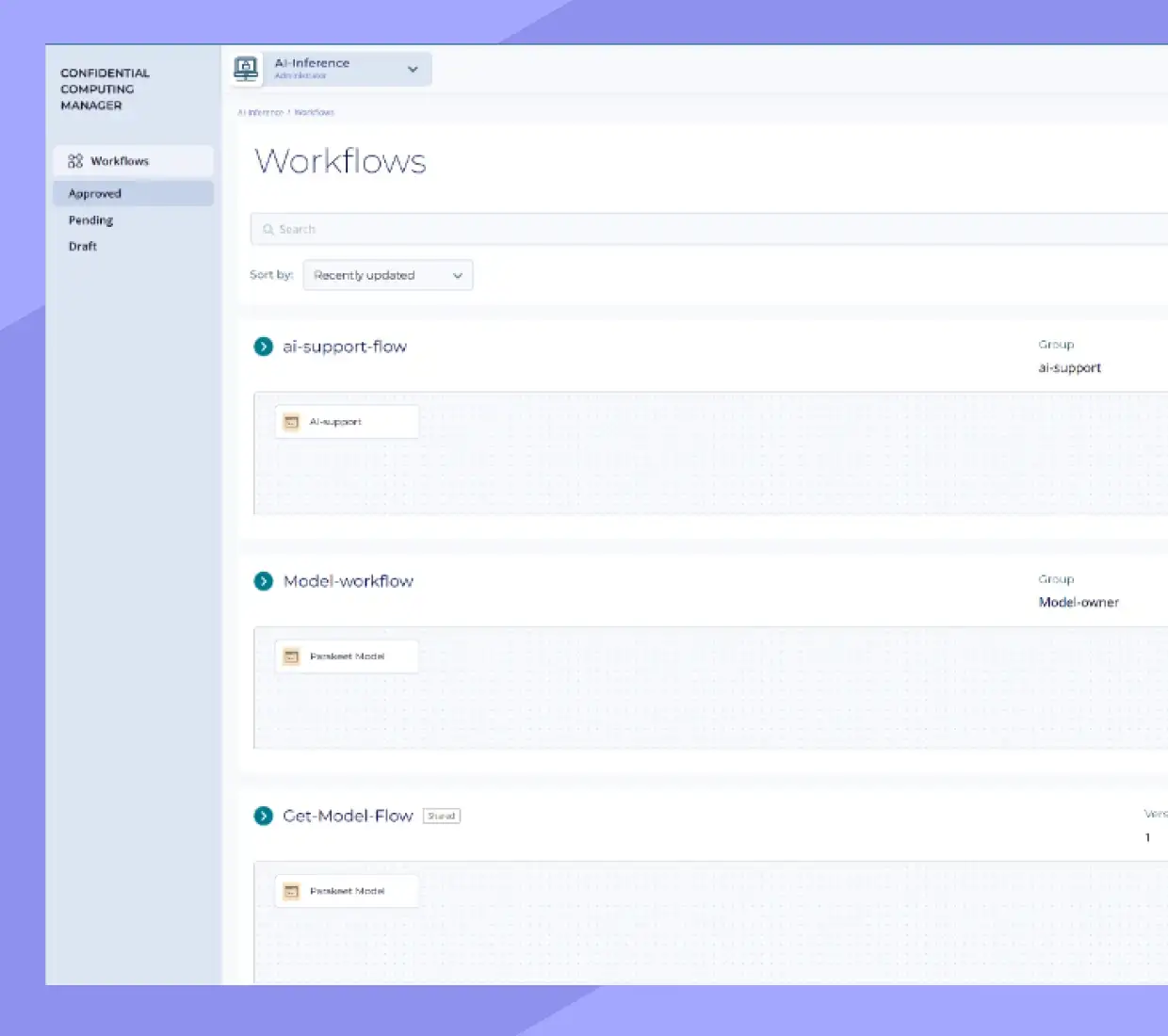
Simplify Operations
Provision, configure, and monitor your entire Confidential Computing infrastructure from one place. Have full control over workflows and policies, eliminate management complexity and fragmented tooling, and uphold performance as you scale.
- Available on-premises and as SaaS
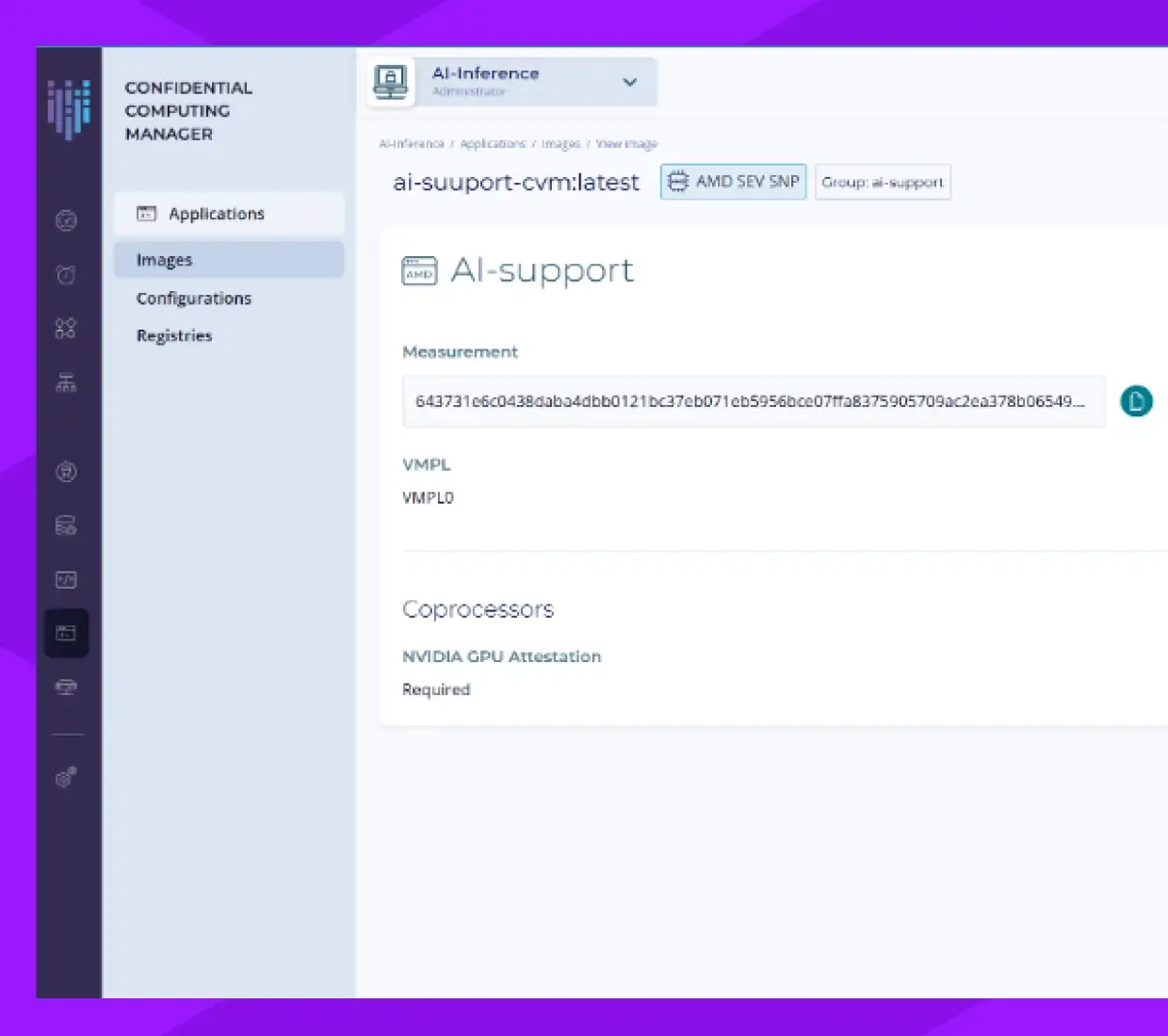
Ensure Consistent Security
Verify firmware and software integrity from a unified control plane before signaling secure key release. Composite attestation across CPU and GPU to ensure no gaps exist between independently managed components.
Supported TEEs:
- Intel TDX and AMD SEV-SNP CPUs
- NVIDIA Blackwell and Hopper GPUs
Enable Confidential AI
Create a secure, on-demand work environment, infrastructure, software and workflow orchestration, that maintains the privacy compliance required by your organization. Safely use AI to grow and innovate and keep sensitive data and frontier models secure with Confidential Computing.
Benefits

Ensure data and model weights are never exposed, eliminate insider threats, and close the attack surface across the full inference lifecycle

Cryptographic proof of data isolation at the hardware level satisfies GDPR, HIPAA, and data sovereignty requirements, turning compliance bottleneck into a built-in guarantee.

Run AI entirely on your own terms with zero-trust architecture. Have full control over deployments, data access, and model choices.
Resources
Here are some of latest news, blogs, resources, events, and more