Do you know how understanding your company’s data can benefit you?
Understanding your company's data has several advantages, such as better decision-making and higher returns on investment. It may, for example, help you foresee prospective losses and track your company's overall performance.
There has been a significant investment and innovation in the field of cryptology in recent years; this blog examines some of the developing technologies and solutions that have the potential to change cryptology for the next decade and beyond - Private Multi-Party Analytics (MPA).
We developed a list of the top 10 reasons why firms are now investing in Private Multi-Party Analytics to get a sense of what's going on.
Ready? Let's dive right into it.
Private Multi-Party Analytics in the Business world:
A great example of long-term research success is Private Multi-Party Analytics, throughout the first 20 years of multi-party analytics research, there were no applications in sight, and it was uncertain whether Private Multi-Party Analytics would ever be used. In the recent decade, the utility of Private Multi-Party Analytics has altered substantially.
Aside from becoming fast enough to be used in practice, Private Multi-Party Analytics has also earned industry recognition and transformed into a technology that is used in practice at the present moment.
Private Multi-Party Analytics is an approach to cryptography that allows two or more parties to perform a computation utilizing their private data without disclosing that data to the other party in question.
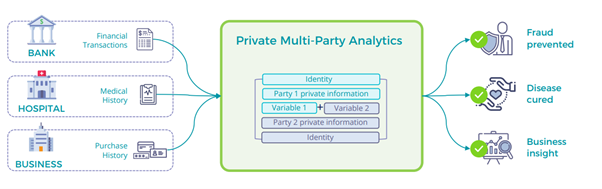
Fig 1: Businesses are using this technology to improve online authentication, identification, and key management
Business transactions and project collaboration necessitate the exchange of information among multiple parties. A lot of times, the information that's being exchanged is confidential. Personal data, such as bank account numbers, social security numbers, and other identifiers, may be included. For both public and private organizations, unauthorized access to data is a necessity.
IT infrastructure operators and engineers, security architects, business consultants, and data scientists may be able to access your information without unauthorized access in some instances.
Organization’s ability to use machine learning in healthcare has grown tremendously as they've gained access to larger datasets and images of patients taken by medical devices. Multiple data sources aid in disease diagnosis and therapeutic development. By exchanging patient medical records with a centralized, trusted execution environment, hospitals and health institutes can interact (TEE).
The TEE's machine learning services collect and analyze data. This aggregation of data can lead to more accurate predictions due to the use of consolidated datasets for training models. Patients' privacy can be better protected in hospitals thanks to the use of confidential computing.
Listed below are the top 10 reasons why businesses are investing in Secure Multi-Party Computation (Private Multi-Party Analytics) in 2022:
Reason 1: Refuse to Make Compromises on Data Privacy
For firms that wish to use their data, data privacy and utility is a crucial trade-off, especially given the incidence of data breaches and rules such as GDPR and the California Consumer Privacy Act.
Securing sensitive data while still allowing businesses to derive insights from it is one of the most important achievements of modern cryptography, known as secure multi-party computation (Private Multi-Party Analytics).
It is not necessary to compromise on privacy in order to make better use of data. To keep data private, there's no need to hide or remove any functionality.
Privacy is not compromised by using all of the features in the analysis as a way to address the difficult trade-off between data privacy and data utility for a wide range of use cases, privacy-enhancing technologies integrate important privacy concepts into the data life cycle from the beginning to the end.
Private Multi-Party Analytics s goal is to make it easier for people to share information more freely while also protecting their privacy and security in unexpected ways.
Reason 2: It's ready for the commercial market
Even though Private Multi-Party Analytics has theoretically been conceivable for many years, the computational power required has only lately been available. No longer a fantasy, Private Multi-Party Analytics has been demonstrated to be possible.
With secure sharing of data, customers can now better detect financial fraud, aggregate model characteristics across private datasets, and more. Using Private Multi-Party Analytics in production is widespread today. Not only in the Data Science community but also in the Data Privacy community, this has fast become a preferred method for solving real-world challenges
Reason 3: It merely shows the ultimate outcome
Only the final result is revealed by Private Multi-Party Analytics; no information about the computing process itself is revealed. Private Multi-Party Analytics provides a higher level of security than federated learning, a machine learning approach in which data is not gathered but model parameters are exchanged.
With the help of Private Multi-Party Analytics, many parties can work together on a collaborative computation without revealing their private data to each other. Private Multi-Party Analytics allows competing parties to gain knowledge from their pooled data without disclosing it to one another. Nobody has access to another party's data; all they get is the computation's result, which they can use to make crucial decisions.
Reason 4: Private Multi-Party Analytics is less resource-intensive than its counterparts
It takes less computational power to encrypt data using Private Multi-Party Analytics than it does to encode it using fully homomorphic encryption. Fully homomorphic encryption is too slow in its current form.
Fully homomorphic encryption (FHE) is a relatively new development in the field of data encryption and utility. The Private Multi-Party Analytics Technology is intriguing, and we may expect to see faster versions of it for a wide range of applications.
Reason 5: There is no longer a need to trust a third-party
A trustworthy third-party is no longer required to keep the data safe and broker exchanges: Clients never send or receive data outside of their own private network perimeter. In order to unlock its full commercial, scientific, and societal potential, Private Multi-Party Analytics is designed to extract data value while protecting the privacy and security of this information.
Private Multi-Party Analytics is designed to guard against two types of attacks: adversarial and internal. It is impossible for anyone to derive details about a user's personal data from the output. There must be no way for an antagonistic party to keep other parties from receiving their correct outputs.
Those that try to disrupt the computation are called adversaries in this context. Other parties' private information may be obtained, or the computation's output may be tampered with as part of the attack.
Reason 6: GDPR and sovereign data privacy compliance
Secure multiparty compute solution satisfies and exceeds standards for international data transfer GDPR and sovereign data privacy compliance (because the data never moves). Consumers' privacy is routinely violated by hackers, businesses, and even governments, despite the existence of data privacy regulations designed to prevent such violations, such as the General Data Protection Regulation (GDPR) in the European Union and the California Consumer Privacy Act (CCPA).
This is becoming more prevalent as businesses are increasingly sharing the data of their customers with third-party or organizations in order to improve their services, acquire new insights, or generate revenue from their data assets. Private Multi-Party Analytics enables enterprises to make use of the ever-increasing volume of data while maintaining the confidentiality of any private or sensitive information they collect.
Reason 7: Private Multi-Party Analytics has High Accuracy & Precision:
For the crypto community, accuracy and precision are of the utmost importance, and the first 2 decades of research on Private Multi-Party Analytics we primarily focused on the practicability of the concept.
Additionally, there were concerns about how to describe and show security for different adversarial and networking models, as well as the possibility of achieving Private Multi-Party Analytics under certain conditions. During the next decade, a great deal of attention was paid to how Private Multi-Party Analytics might be made even more successful.
The first components of this technique were entirely algorithmic and focused on restricting the extent to which the cryptographic natives may go above and beyond what was necessary. Concerns concerning the memory and correspondence, the use of equipment guidelines like AES-NI and then some others were considered after this.
As of right now, the results of Private Multi-Party Analytics fulfill and even exceed the expectations of the client in terms of accuracy and precision.
Reason 8: Private Multi-Party Analytics is Quantum-Safe!
Modern cryptography's fundamental primitives include secret sharing and multiparty computation, which is also known as "secure function evaluation." These primitives make it possible for a group of players who do not trust one another to carry out correct, distributed computations on the sole assumption that some of the players will follow the protocol honestly.
Because the data is fragmented and dispersed across participants (or "secret shared") throughout the calculation, it is considered to be encrypted while it is in use. This prevents the data from being vulnerable to quantum attacks.
Reason 9: Remove the Potential for a Single Point of Failure in Key Management
One of the most common uses for Private Multi-Party Analytics in the realm of information security is to protect cryptographic keys from being stolen or misused. This is accomplished by ensuring that the keys are never exposed in a single location at a single point in time and by enforcing usage policies across multiple entities.
This makes it possible to safeguard cryptographic keys within the software, giving an alternative to outdated hardware systems that present a number of operational issues in today's hybrid and multi-cloud scenarios.
Reason 10: The world is moving toward dMPC!
Security concerns are rising among investors and custodians of digital assets, including digital asset exchanges and institutional funds, as cryptocurrency prices have reached all-time highs.
This has led to an increase in the demand for the best feasible wallet and transaction encryption and security solutions for digital asset custodians.
Just as Bitcoin eliminates the third party in transactions, Private Multi-Party Analytics may eliminate the third party in private key management. Decentralized consensus is needed to ensure that the Private Multi-Party Analytics protocol does not fall victim to the same security and settlement delays as decentralized private key management.
Private Multi-Party Analytics liberates digital assets from these issues, allowing them to be staked, borrowed, or exchanged in the rapidly expanding DeFi ecosystem.
How does Fortanix lead the Private Multi-Party Analytics market?
Fortanix® is the data-first multi-cloud security company. As the industry’s first and largest provider of confidential computing solutions, Fortanix decouples data security from infrastructure. Fortanix solutions empower organizations with centralized controls to secure data spread across clouds, applications, SaaS, databases, and data centers.
Over a hundred enterprises worldwide, especially in privacy-sensitive industries like healthcare, fintech, financial services, government, and retail, trust Fortanix for cloud security and privacy.
Fortanix Private Multi-Party Analytics Solution:
Sharing sensitive data without exposing it to other parties or breaking privacy standards is made simple and secure by Fortanix. In an enclave, which is a trusted execution environment, a variety of parties can submit encrypted data, and the data is pooled, analysed, and the results are then exported in an encrypted manner back to each party with the analytics results. Encryption ensures data security throughout the whole process, from the transmission to computation to storage.
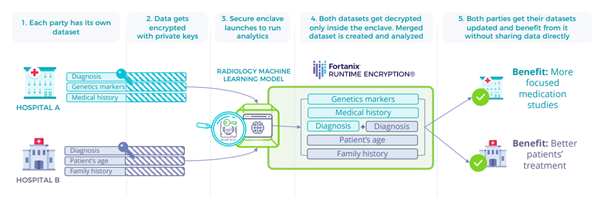
Any scenario in which multiple parties need to combine and analyze their private data without disclosing the underlying data or machine learning models to any of the other parties can benefit from private multi-party analytics. This type of analytics can be applied in any situation in which multiple parties have private data.
The technology may be utilized in the prevention of fraud in the financial services industry, the identification of diseases or the development of treatments for those diseases in the healthcare industry, or the acquisition of business intelligence.
After all, is said and done:
A better society is one where security and privacy aren't sacrificed for convenience, and where people are empowered and in control of their own personal data. This is why we feel that these technologies should be used widely in the future.
Companies and organizations can use these strategies to safely exchange and learn from data without compromising the privacy, safety, or well-being of anybody else.
In order to make Private Multi-Party Analytics feasible on big data sets and for complicated issues, and to make it easy to use for non-experts, additional research breakthroughs are needed. A bright future for Private Multi-Party Analytics in practice is painted by recent accomplishments and the vast amount of applied research already being generated.
Applied Private Multi-Party Analytics solutions by firms such as Fortanix, will have solid scientific foundations thanks to ongoing theoretical development in Private Multi-Party Analytics.
Check our solution brief on Multiparty Collaboration.









