AWS Policy Change and the Hidden Data Security Risk
On 22nd December 2021, AWS deployed a new version (v20) of AWSSupportServiceRolePolicy—used by a mandatory role for AWS Support access to all AWS Accounts.
In this policy, they added the action ‘s3:getObject’ which granted complete access to all customer data to the AWS support teams.
Note: AWS has now reverted the change, and the potential risk now stands mitigated.
Yes, you heard it right. A small policy change rollout internally by AWS gave access to your data in S3 buckets to the AWS support teams. This incident shows how a data breach risk can appear suddenly, even without malicious intent.
Lessons Learned from the December 2021 AWS Security Incident
Let us take a moment and reason this incident critically. Security incidents are not new, and neither are data breaches and ransomware attacks Worst case scenario - your S3 data could have been accessed by AWS Support teams if they really wanted to.
Sensitive data getting into the wrong hands is not new, then what is new about this incident? This security incident was not deliberate. That’s new. So, here are a few nuggets that we can learn from this incident:
- Despite of all defensive measures such as IAM, firewalls, end-point agents, your data is still vulnerable to human error.
- Not all data breaches stem from felonious intentions.
- There is no permanent panacea to data breaches.
Fortunately, there are steps that you can take now to shield yourself from such threat vectors – intentional or unintentional.
The objective is to keep your data encrypted in a way that allow you, and only you to control who can and cannot decrypt/access your data.
Here are a few ways to mitigate data breach risk:
- Encrypt your data before storing it in cloud storage services such as AWS S3. In other words, use client-side encryption if you can.
- If you have reasons that discourage you from using client-side encryption, then at least use keys that you can manage such as AWS Customer Managed Keys (CMK), which allows you to separate the key permissions from the storge service permissions, such as S3.
- Continue using your incumbent security solutions. We believe layered defense is always the best strategy. We have 7 layers of defense in our own solution!
Note that even if the data was encrypted using AWS managed keys, this security event couldn’t have been prevented. Why so?
Because with proper IAM access, which was the case here, the data would have been seamlessly decrypted if AWS support teams had tried to access it.
How Fortanix Helps Protect Data Across Cloud Environments
Fortanix is a data first company, and we empower you to protect your most important asset first - your global data, from one centralized place and give you unmatched control of your data security across public, private, and hybrid clouds, all that with an easy-to-use, automation-friendly solution loved by developers, security teams, and auditors.
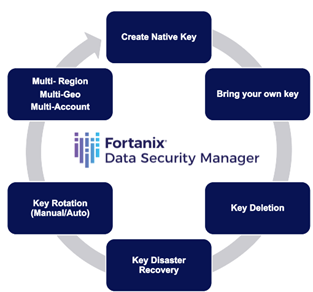
Our flagship product DSM Cloud Data Control lets you manage the entire lifecycle of AWS Customer Managed Keys as well as for other clouds from a single pane of glass.
It also empowers you to import (BYOK), automatically rotate, schedule delete, or delete the key material on demand – Kill Switch.
Not only that, but you can also manage the AWS key policies as well as apply your own custom policies using our award-winning UI or rich APIs.
Along with that, if you wish to do client-side encryption, then also we have you fully covered. We offer a rich set of APIs – REST, PKCS#11, KMIP, JCE, Microsoft CAPI and CNG.
If you would rather integrate your applications via SDKs, then we offer Java, Python, Go, C#, .NET, Javascript/Node.js and PHP.
Net-net, we need to understand that data breaches won’t stop. You must take full control of your data wherever it goes. Our security platform with its plethora of inbuilt tools and technologies can help you secure and control your data at-rest, in-transit and in-use.
We are also the leaders in Confidential Computing. However, you must act now. Our SaaS Trial only takes 5 minutes to setup. Try it out today, and don’t let such breaches spoil your Holiday! Happy Holidays!










