Overview
Like most other cloud service providers, Amazon Web Services (AWS) offer their own cloud-native key management service to generate and manage master keys. But the native key management comes with its own shortcomings. Some of the drawbacks are as follows:
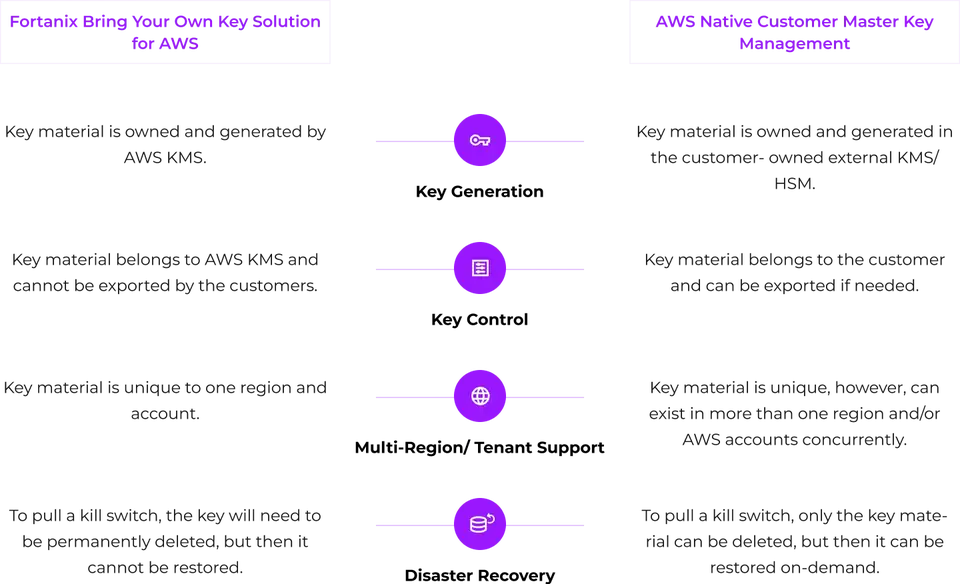
- The cloud provider owns the key material, and the key can only be used in one cloud and typically for a single tenant. If a master key is deleted, then there is no way to get that key back. Any data encrypted under that key is lost.
- No consistent way of setting fine-grained controls over key management policies across multi-cloud.
- Customers do not get a single pane of glass for multi-geo and multi-cloud key management. The policy framework and auditing will be different for every cloud.
Solution Overview
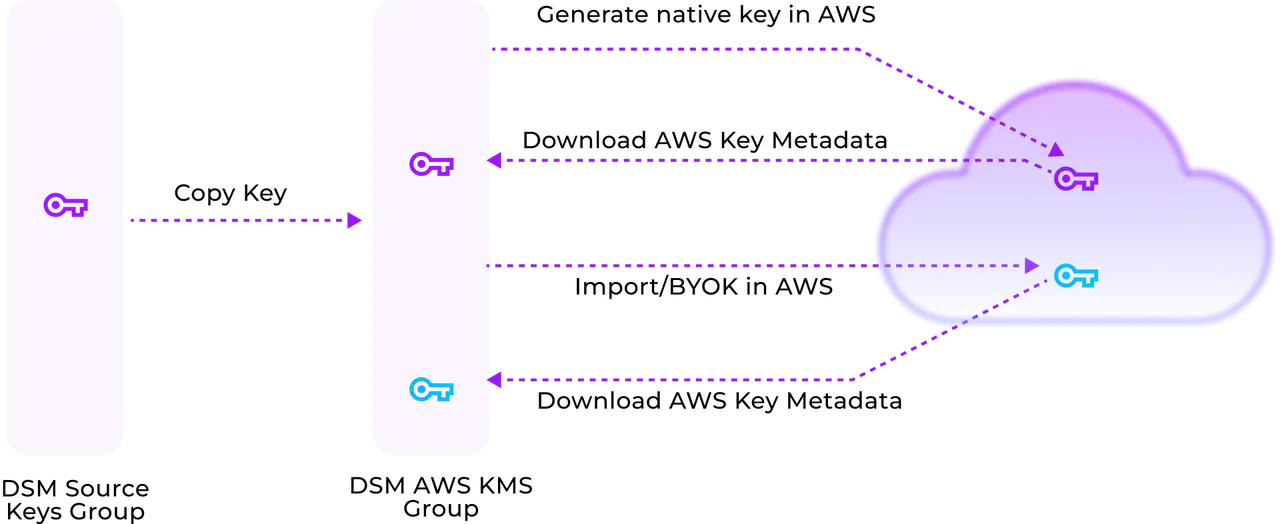
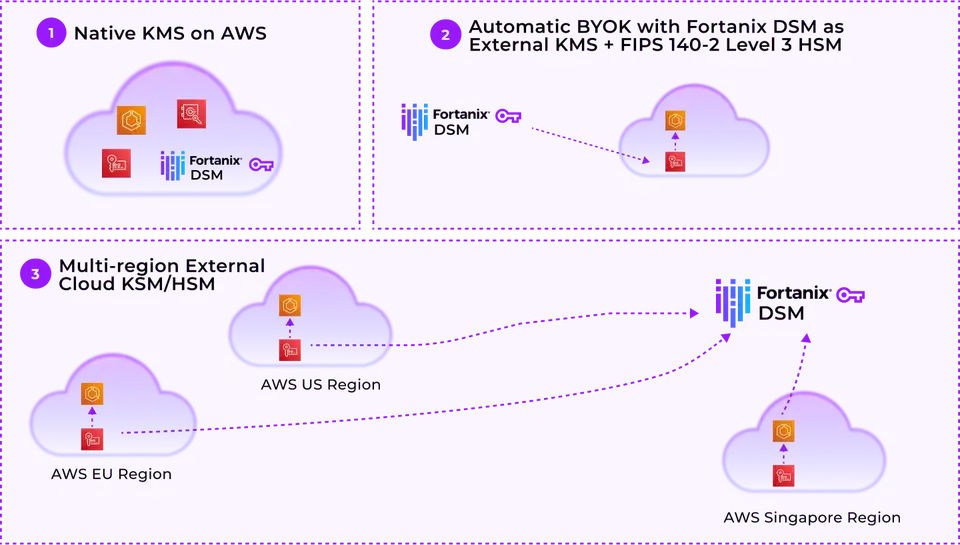
The Fortanix solution for AWS Key Management offers complete automated Bring Your Own Key (BYOK) and lifecycle management for management and automation of native AWS KMS keys (CMK - Customer Master Key) and allows users to manage all keys centrally and securely.
This enables AWS users to bring or import their own master key, which AWS stores in their key management system and encrypts all Data Encryption Keys (DEKs) under that key—providing greater control over their data and keys.
Why Fortanix?
The Fortanix solution for AWS Key Management offers complete automated Bring Your Own Key (BYOK) and lifecycle management for management and automation of native AWS KMS keys (CMK – Customer Master Key) and allows users to manage all keys centrally and securely.
This enables AWS users to bring or import their own master key, which AWS stores in their key management system and encrypts all Data Encryption Keys (DEKs) under that key—providing greater control over their data and keys.
Fortanix Data Security Manager allows organizations to Bring Your Own Key (BYOK) for AWS cloud. With this approach customers bring or import their own master key, which AWS stores in their key management system and encrypts all Data Encryption Keys (DEKs) under that key. This provides customers with greater control over their data and keys.
Fortanix DSM Use Cases for AWS
Key Benefits

Get Full Control Over Keys
Customers can bring or import a master key which the AWS stores within its KMS. This allows customers to retain owner- ship of the master key material and have greater control over the data stored in AWS.

Easily Manage AWS Key States and Operations
Fortanix helps customers easily manage the AWS key states and operations as the same nomenclature of AWS KMS is used in Fortanix AWS KMS integrations. Also, a customer can author AWS key policies from Fortanix.

Stop Data Breaches With Kill -Switch
Gives you a central kill -switch and a fully managed disaster recovery for all your keys. Key material can be deleted from Fortanix to make an AWS key in “Pending Import” state and stop data breaches. Key material can also be reclaimed by importing it back into the cloud KMS.

Secure Data Across Locations and Regions
Offers greater flexibility as the same keys can be used to secure data across multiple accounts, locations, and regions.

Manage Multi-Cloud Keys From a Single Pane
Fortanix Data Security Manager allows you to manage and control multi-cloud keys in a completely cloud agnostic way. Organizations can keep full custody of their keys in a FIPS 140-2 level 3 certified HSM.

Get Centralized Control and Audit of Keys
Fortanix Data Security Manager enables organizations to apply cen- tral control and audit the keys using quorum approvals and audit logs.
How does the Solution Work?
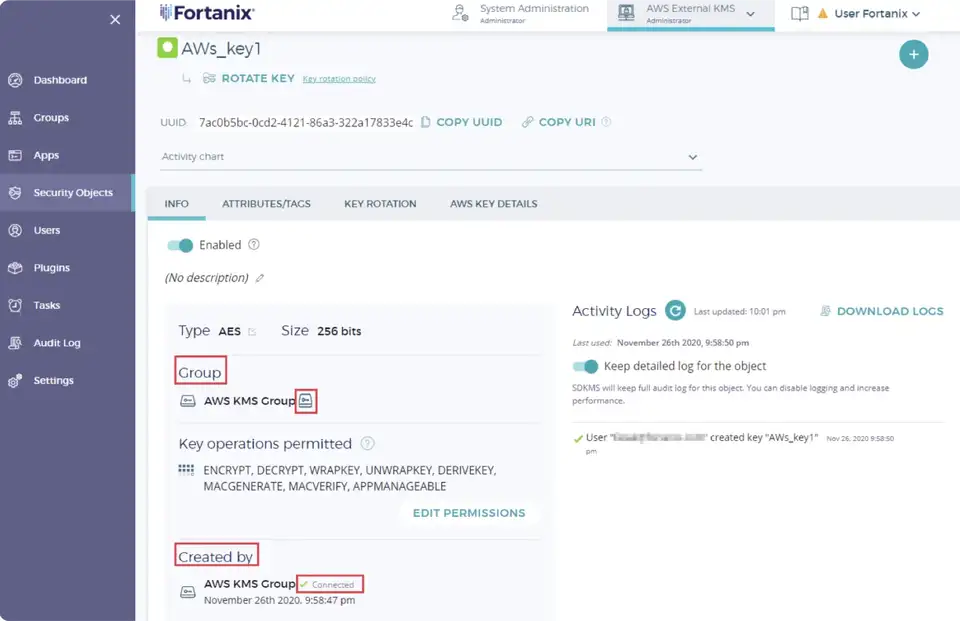
An AWS KMS group is created in the Fortanix DSM account, and this group is configured to interact with the AWS KMS. After the AWS group successfully connects to the AWS KMS using the connection details, the keys from the AWS KMS are stored in the Fortanix DSM AWS group as virtual keys. A virtual key is a key whose key material is not present in the AWS group. The key material is stored securely in the AWS KMS.