The Problem
Each cloud vendor offers unique cloud key management solutions for their platforms. With this approach, it is impractical for organizations to implement integrated data security across several Cloud Service Providers (CPSs).Instead, organizations end up with multiple proprietary Key Management System (KMS) solutions, resulting in key sprawl. There is a high risk to lose track of where keys are, who accessed them, when, and from where.
In addition, organizations should keep custody of their keys and not implicitly trust the CSP with keys that provide access to their most sensitive data that is hosted there. Applying such Zero Trust principles enables them to comply with data privacy and security regulations such as the GDPR/Schrems-II. When cloud providers have key custody of keys, they can also access the data.

Fortanix Solution
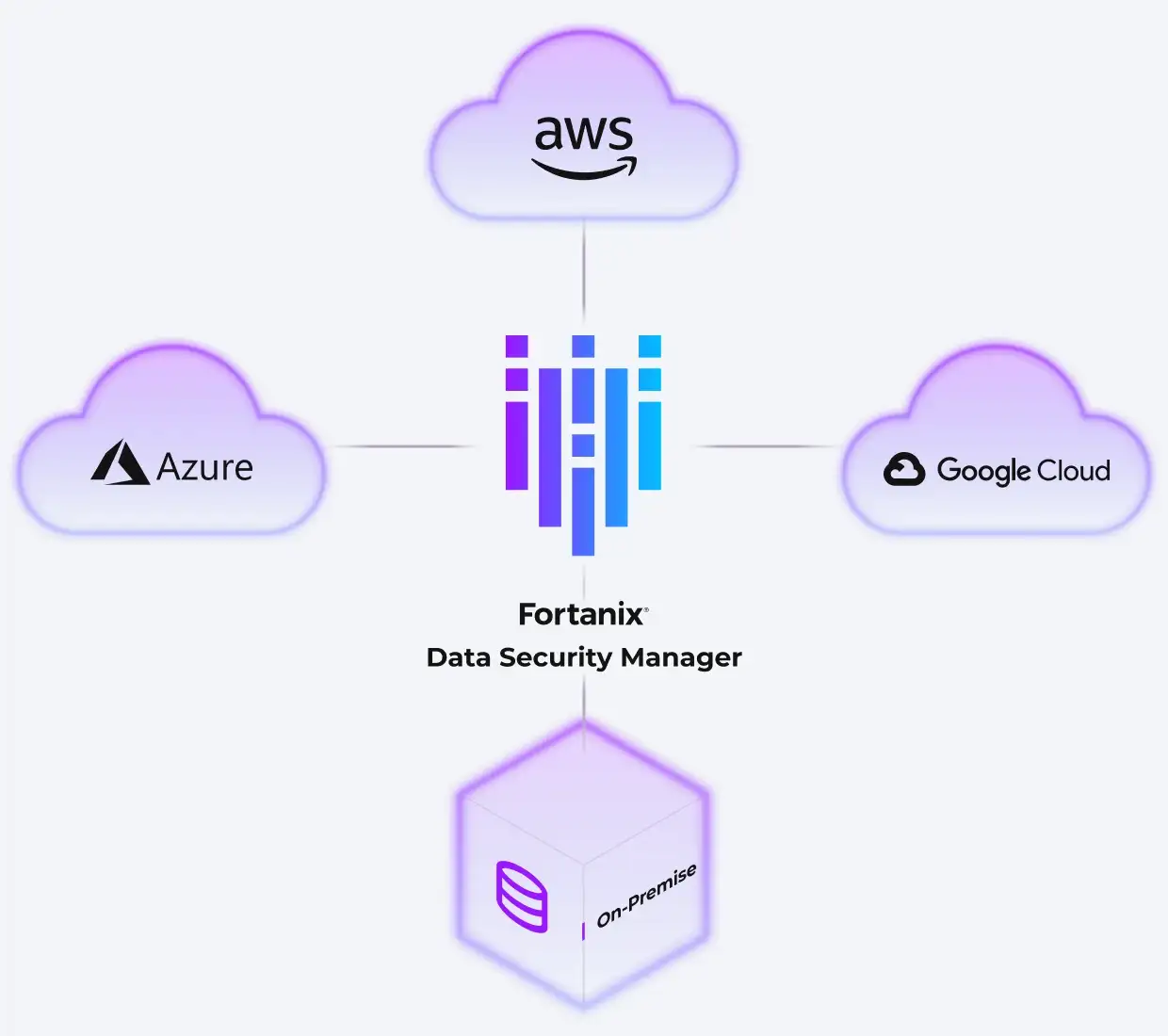
The Fortanix solution seamlessly integrates with hybrid and multicloud key management services to enable organizations to centrally manage the lifecycle of all keys, from a single interface, no matter if these keys are used on-premises, or in the cloud.
Encryption keys are always under organizations' control and can be stored on highly secure, FIPS 140-2 level 3-certified HSMs. This multi cloud SaaS key management solution offers Bring Your Own Key (BYOK) and Bring Your Own Key Management Service (BYOKMS), allowing organizations to segregate their keys from the data.
With Fortanix DSM, organizations can centrally define and enforce granular, uniform access control policies.
Benefits

Fortanix provides a centralized, single point of control and management at scale across hybrid and multicloud environments. Organizations can manage encryption, key management, secrets management, and tokenization for every cloud and on-premises system. With Fortanix, organizations get consistent policy management and enforcement across clouds, and geographic regions.

Regulations such as GDPR and Schrems-II require organizations to ensure their keys are stored separately from the data. Fortanix DSM provides protected storage for encryption keys in highly secure, FIPS 140-2 Level 3-certified HSMs. With a centralized data security platform, organizations can easily prove to auditors that their keys do not cross the boundaries of the European Economic Area, for example.

DevOps and Security teams must collaborate to ensure data privacy. All security functions are supported as RESTful APIs for easy integration into cloud-native tools and technologies. Using a REST API, they can implement efficient secrets management, integrate cryptography into applications in the coding phase, and tokenize sensitive data.
The Fortanix Difference

Unified platform for Data Security
A centralized SaaS solution to simplify and strengthen data security across hybrid and multicloud environments.

DevOps ready
Fortanix DSM easily integrates into automation workflows with REST API support.

Highly Secure
Granular access control, including quorum approval, for keys and certificates which stay safe in FIPS 140-2 Level 3 HSMs.