Introduction
As the world leader in the deployment of Trusted Execution Environments, Fortanix enables B2C businesses to secure cryptocurrency wallets while bundling additional functionality with them which makes them more secure and Custodial.
The Fortanix “Custodial Warm Wallet” solution provides an additional layer of security to cryptocurrency wallets by incorporating a second factor of authentication (2FA) using Time-based One-Time Passwords (TOTP).
The solution forms part of the Fortanix Secure Web3 Infrastructure suite of tools and is provided as a managed service.
In this briefing document, we outline the motivations behind our design choices and highlight how our design choices make it easy to incorporate our solution within the backend systems of B2C cryptocurrency businesses.
We comment on how our solution reduces the trust barrier for cryptocurrency businesses trying to acquire new customers.
Today, end users of crypto-currencies have two options; they can either manage cryptocurrency keys by themselves or trust a custodial wallet service provider to do so. Self-management is very inconvenient for novice users. While custodial wallets are easy to use, cryptocurrency businesses are often compromised, and that too by insiders. The Fortanix “Custodial Warm Wallet” solution enables B2C cryptocurrency businesses to ensure that customers’ assets are not trans- ferred without their explicit consent. This assurance reduces the trust barrier towards B2C cryptocurrency businesses. It also reduces operational risks for wallet providers.
Custodial Warm Wallet
The Fortanix Custodial Warm Wallet solution enables B2C cryptocurrency businesses to ensure that their customers’ assets are not transferred without their explicit consent.
Secure 2FA
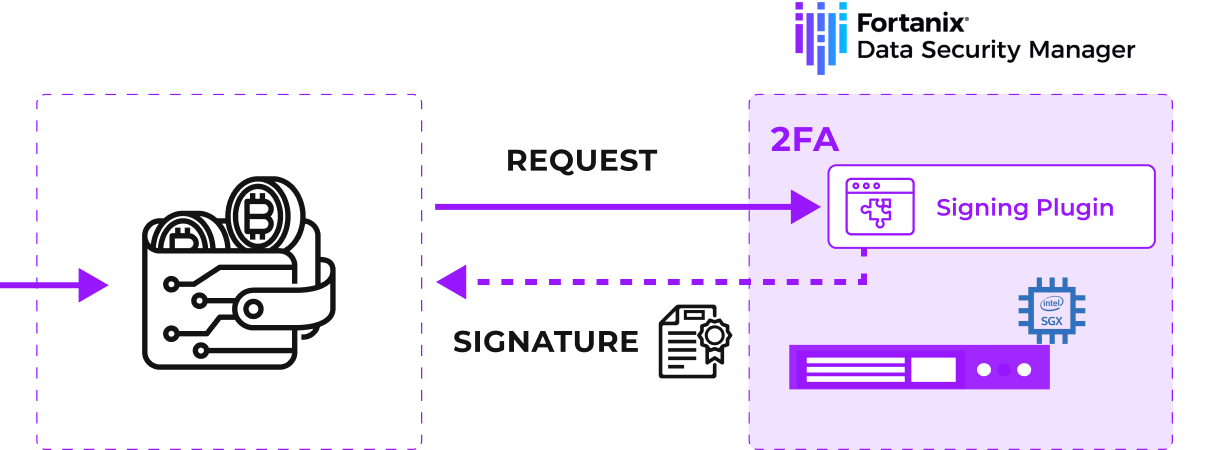
Fortanix DSM (Data Security Manager) SaaS is a FIPS 140-2 Level 3 compliant platform for secure key man- age-ment. It offers a unique security architecture where custom plugins can be developed and deployed to run inside the hardware protected secure environment. The plugin can be protected with a quorum policy that involves multiple admin users. Once deployed, the plugin code cannot be modified without explicit permissions from multiple administrators.
The Fortanix Custodial Warm Wallet solution includes a plugin which combines the transaction signing functionality of a warm wallet and a 2FA system, specifically TOTP. See Figure 2.
Ease of Use
To support easy integration, the Fortanix Custodial Warm Wallet solution includes an SDK (Software Development Kits) module which integrates seamlessly with the web3.js Ethereum SDK.
Secret Zero Problem
While cryptocurrency keys can be managed inside Hardware Security Modules (HSMs), which are highly secure, the application that interacts with the HSM (Hardware Security Module) using an API key is often in an environment which is much less secure. If this application misbehaves or is compromised and the API key stolen, a wallet provider could see heavy losses. This is an instance of the famous Secret Zero Problem; while most of the secrets can be protected inside secure environments, the zeroth secret remains in an environment which may be considered insecure.
One mechanism to improve the security of warm wallets is to implement a 2FA system. Present day 2FA systems are often deployed in insecure environments. I.e., they are often deployed in the same environment as the backend application managing the HSM API keys. See Figure 1. If this insecure environment is breached, the cryptocurrency keys managed by the HSM could be used to sign transactions and this could lead to heavy losses to the custodial wallet provider and their customers.
Figure 1: Typical Warm Wallet solutions implement 2FA systems as part of the wallet backend environment accessible to malicious insiders or outsiders that get past perimeter defence systems. An attacker can gain access to the HSM API key and sign crypto-currency transactions without requiring 2FA from end users.
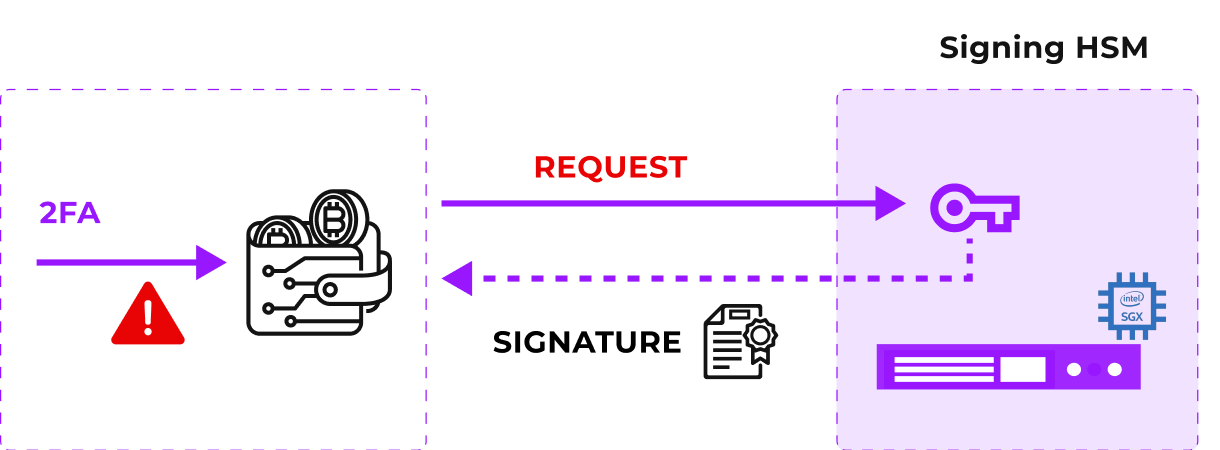
Figure 2: The Fortanix Custodial Warm Wallet solution implements the 2FA system as a Fortanix DSM Plugin. Even if an attacker gains access to the HSM API key, they cannot spend assets that belong to end users because they will not be able to provide a valid TOTP code which is required to sign every transaction.
Top Benefits
The Fortanix Custodial Warm Wallet solution offers several benefits.

Improved Security
By moving the 2FA system to a highly secure environment, we have significantly improved the security of the entire system.

Reduced Trust Barrier
Our solution ensures that a compromised wallet backend system does not lead to loss of end user’s assets. This means that end users can trust wallet providers more.

Reduced Operational Risk
Our design reduces operational risk dramatically. Cryptocurrency businesses can demonstrate to regulators, insurance providers or other authorities that users’ assets cannot be spent without their involvement.










