Artificial Intelligence (AI) and Machine Learning (ML) have emerged as revolutionary forces across the finance, defense, education, and healthcare industries.
These transformative technologies extract valuable insights from data, predict the unpredictable, and reshape our world. However, striking the right balance between rewards and risks in these sectors remains a challenge, demanding our utmost responsibility.
As we find ourselves at the forefront of this transformative era, our choices hold the power to shape the future. We must embrace this responsibility and leverage the potential of AI and ML for the greater good.
Nevertheless, we must navigate the complex terrain of data privacy concerns, intellectual property, and regulatory frameworks to ensure fair practices and compliance with global standards.
Let us understand the data privacy challenges associated with AI and how Fortanix helps organizations address these challenges through Confidential Computing.
Data Privacy Challenges in AI
Artificial intelligence relies heavily on vast data to train and improve models. This data often includes personally identifiable information (PII), financial records, medical histories, and other sensitive information.
Organizations face the following data privacy challenges in the context of AI.
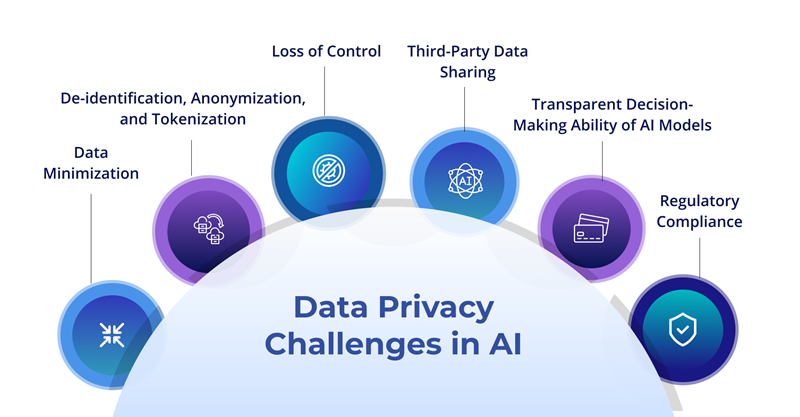
- Data Minimization: AI systems can extract valuable insights and predictions from extensive datasets. However, a potential danger exists of excessive data collection and retention, surpassing what is essential for the intended purpose. In AI applications, the principle of data minimization holds the utmost importance and advocates collecting and retaining only the minimum amount of data required.
For example, a mobile banking app that utilizes AI algorithms to offer personalized financial advice to its users collects information on spending habits, budgeting, and investment opportunities based on user transaction data.
However, instead of gathering every transaction detail, it must focus only on key information such as transaction amount, merchant category, and date. This approach will allow the app to provide financial recommendations while safeguarding user identity.
- Third-Party Data Sharing: AI systems heavily rely on data from multiple sources, including third parties such as data providers, social media platforms, and public databases. For instance, a virtual assistant AI may require access to a user's data stored by a third-party app, like calendar events or email contacts, to provide personalized reminders or scheduling assistance.
Companies often share customer data with marketing firms without proper data protection measures, which could result in unauthorized use or leakage of sensitive information. Sharing data with external entities poses inherent privacy risks.
Maintaining data privacy when data is shared between organizations or across borders is a critical challenge in AI applications. In such cases, ensuring data anonymization techniques and secure data transmission protocols becomes crucial to protect user confidentiality and privacy.
- Loss of Control - When organizations depend on cloud-based AI services, they often encounter difficulties maintaining complete authority over their data.
Consider a healthcare institution using a cloud-based AI system for analyzing patient information and delivering personalized treatment suggestions. The institution can benefit from AI capabilities by utilizing the cloud provider's infrastructure.
However, the healthcare institution cannot trust the cloud provider to handle and safeguard sensitive patient data. The absence of direct control over data management raises concerns. Although cloud providers typically implement strong security measures, there have been cases where unauthorized individuals accessed data due to vulnerabilities or insider threats. - Transparent Decision-Making Ability of AI Models - Customers need to understand the reasoning behind the decisions affecting them. Developing methods that provide insights into decision-making can establish trust between AI systems and customers.
For example, traditional models lack transparency in the context of a credit scoring model, which determines loan eligibility, making it difficult for customers to comprehend the reasons behind acceptance or rejection. Confidential Computing can help overcome this challenge by enabling AI models to operate on encrypted data, preserving privacy while explaining decisions.
- De-identification, Anonymization, and Tokenization: Re-identification attacks can potentially link supposedly anonymized data back to specific individuals. For instance, consider a healthcare organization that shares de-identified patient data with researchers. Despite removing direct identifiers, an attacker could combine this data with publicly available information or employ advanced data linkage techniques to successfully re-identify individuals, compromising their privacy.
Tokenization can mitigate the re-identification risks by replacing sensitive data elements with unique tokens, such as names or social security numbers. These tokens are random and lack any meaningful connection to the original data, making it extremely difficult re-identify individuals.
- Regulatory Compliance: Stringent data protection regulations, such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA), impose strict obligations on businesses to ensure the security of personal data.
These regulations vary from region to region, while AI models deployed across geographies often remain the same. Regulations continuously evolve in response to emerging trends and consumer demands, and AI systems struggle to comply.
Consequently, these models may lack the necessary features to meet the specific requirements of a particular state's laws. Given the dynamic nature of these regulations, it becomes challenging to adapt the AI models continuously to the ever-changing compliance landscape.
Fortanix Confidential AI
Introducing Fortanix Confidential AI, an advanced solution that empowers data teams to effectively use sensitive data and leverage the full potential of AI models with utmost confidentiality. It creates a secure and reliable work environment that meets the ever-changing requirements of data teams.
Related Read: Announcing Fortanix Confidential AI: Building Better AI Models While Preserving Privacy
Benefits of Confidential AI
1) Proof of Execution and Compliance - Our secure infrastructure and comprehensive audit/log system provide the necessary proof of execution, enabling organizations to meet and surpass the most rigorous privacy regulations in various regions and industries.
2) Utilize Private Data for Productive Insights - The availability of private data plays a vital role in enhancing current models or training new ones for accurate predictions. Private data that may initially seem inaccessible can be securely accessed and utilized within protected environments. By employing Confidential Computing at different stages, the data can be processed, and models can be constructed while maintaining confidentiality, even during data in use.
3) Safeguard AI Models Deployed in the Cloud - Organizations must protect their developed models' intellectual property. With the growing prevalence of cloud hosting for data and models, privacy risks have become more complex. Fortanix C-AI simplifies securing intellectual property for model providers by enabling them to publish their algorithms within a secure enclave. This approach guarantees that cloud provider insiders have no access to or visibility into the algorithms.
4) Seamlessly Deploy and Provision Using a Managed Service: Given the limited practical experience and insight into technical infrastructure provisioning, data teams require a user-friendly and secure infrastructure that can be readily activated for analysis. Fortanix C-AI offers a hassle-free deployment and provisioning process, accessible as a SaaS infrastructure service with no need for specialized expertise.
5) Expedite Project Sign-Off- Organizations can streamline the project authorization process by leveraging the world's pioneering, secure, confidential computing infrastructure, purposefully developed to facilitate AI execution and deployment. It enables swift sign-off from security and compliance teams.
6) Trusted Vendor - Fortanix, an established vendor, is renowned for its impressive track record of delivering cutting-edge security solutions. When it comes to Confidential Computing, there is no better partner than Fortanix, the industry leader in this field. Our visionary approach has led to introducing and defining the runtime encryption technology, which has completely transformed the data security landscape.
How Confidential AI Works?
Related Read:
Managing Risk and Ensuring Compliance with Confidential Computing
How Explainable AI (XAI) and Confidential Computing Break Open the AI Black Box?
Learn more with a practical demo. Connect with our experts for a free assessment of your AI project infrastructure.










