Security systems across cloud and infrastructure are built on cryptographic keys that enable encryption, authentication, signing, secure communication, and more. When strengthening cryptographic security posture, the focus is often on stronger algorithms, such as moving from RSA-2048 to RSA-4096, adopting elliptic curve cryptography, or preparing for post quantum algorithms.
This is important and necessary. Another important element in this broader picture is the randomness used during key generation, since cryptographic key material is derived from random input.
Because randomness ultimately originates from entropy sources, Fortanix DSM supports the use of external entropy sources alongside internal ones to further strengthen the security posture in this area.
RNG in Fortanix Data Security Manager (DSM)
The component responsible for generating random bits is generally called a random number generator (RNG). In practice, an RNG is not a single mechanism, but a system made up of multiple components working together to produce the required randomness. Different RNG designs exist, for example, the Linux RNG follows its own architecture and operating model.
NIST also provides a set of recommendations for how such systems should be designed through the SP 800-90 series (90A, 90B and 90C). Fortanix closely follows these recommendations when relevant.
Below is a close approximation of the flow in a Fortanix DSM deployment where external entropy is enabled.
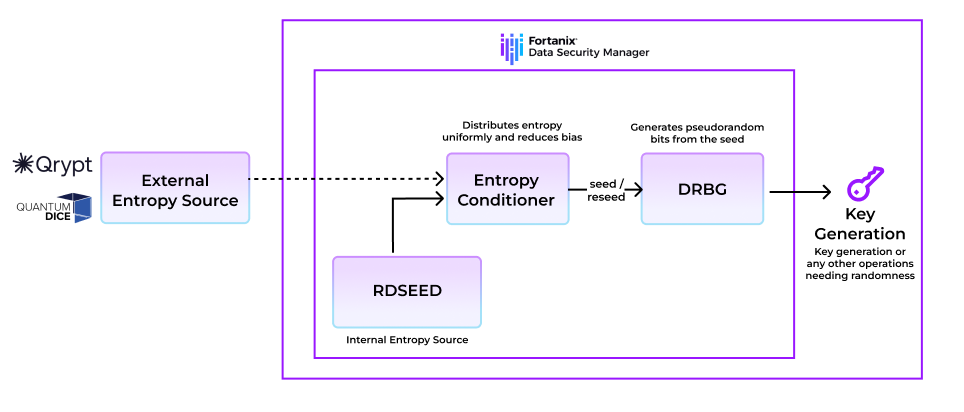
Note that the diagram above is simplified, and the exact details may vary depending on the deployment type.
As shown in the diagram, key generation requires random bits, which it obtains from the Fortanix RNG. While randomness can be drawn directly from an entropy source, entropy sources often cannot supply bits at the rate required by the system.
This is where a Deterministic Random Bit Generator (DRBG) comes in. It takes a small amount of high-quality randomness from the entropy source as a seed and deterministically expands it into a larger stream of bits.
The underlying unpredictability still originates from the entropy source, and the DRBG’s role is to expand that input in a cryptographically secure way. After a fixed number of operations, the DRBG is also periodically reseeded with fresh randomness from the entropy source.
More specifically, the DRBG used here is CTR_DRBG, one of the DRBG mechanisms approved in NIST SP 800-90A. For entropy conditioning, we rely on the derivation function provided as part of CTR_DRBG.
The seed material is obtained from Intel RDSEED, which is Intel’s CPU instruction for obtaining high quality hardware generated seed material from the CPU entropy source, and from the (optionally) configured external entropy source. Entropy from RDSEED and the external source is concatenated and then passed through the conditioning step, which reduces statistical bias and produces a uniformly distributed output that is used as the seed.
Why Entropy Diversification Adds Value
In a modern RNG design, each component has an important role. Entropy sources provide the unpredictability entering the system, conditioning prepares that input for use, and the DRBG expands it into the random bits consumed by the system.
Because entropy is foundational to the security of the construction, the entropy source layer must be of high quality to ensure strong security. As NIST SP 800-90B puts it, “If the noise source fails to generate random outputs, no other component in the RBG can compensate for the lack of entropy; hence, no security guarantees can be made for the application relying on the RBG.”
As noted before, the internal entropy input is provided via Intel RDSEED, which draws from Intel’s high quality hardware entropy source. This hardware entropy source draws randomness from thermal noise, which is a quantum phenomenon. This source has also undergone NIST SP 800-90B entropy source validation, providing strong assurance in the quality of the entropy used for seeding.
To further strengthen this part of the system, Fortanix DSM optionally supports using external entropy sources from providers such as Qrypt and Quantum Dice alongside its internal entropy source to diversify the entropy used for key generation and other operations requiring randomness.
Entropy diversification adds value in two main ways:
- Different underlying mechanisms
Supported external entropy sources derive randomness through mechanisms different from the internal entropy source. This brings in entropy generated in a different way, increasing diversity in the seed material used for key generation. - Reduced dependence on a single source
Bringing in entropy from multiple sources reduces dependence on any one source and can provide added resilience against unforeseen issues in a single source.